Core Component
This application’s functionality is primarily furnished by one or more plug-ins that are based on a core component.
The core component is composed of two subcomponents:
-
A component called LDAP that provides a Java GUI for plain LDAP functionality.
-
A component called Framework that provides a framework for a customizable and extensible Java GUI. Its main focus is on managing hierarchically-structured nodes, particularly LDAP nodes.
"Extensible" refers to the plug-ins. Although plug-ins are in no way restricted to this feature, they typically deal with advanced LDAP functionality like schema management or with functionality for rather sophisticated data models that are based on LDAP (like privilege-based access management or synchronization workflows).
Refer to the About dialog in the Help menu to see what plug-ins you have installed.
This chapter provides information about the core component, including:
-
Information about LDAP in general.
This section is not intended to supersede the comprehensive literature that is available on this topic. -
The basic patterns the core component makes available to the plug-ins and uses itself for the LDAP functionality it provides.
-
Some hints on possible pitfalls.
Using LDAP
(a brief introduction)
LDAP specifies a "directory access protocol". A directory accessible through LDAP stores information about users (for example, their names, their email addresses, their phone numbers, the department they belong to, and so on) and groups of users in many cases, but can also be used to store any other kind of information you can think of. There are two main reasons that explain why you frequently encounter LDAP directories in the Internet and extranet environments:
-
LDAP means that the information in the directory can be accessed and managed through a standardized method specified in a series of internet standards, e.g. http://www.ietf.org/rfc/rfc2251.txt.
-
LDAP directories are optimized for fast read access by numerous concurrent applications in large distributed environments.
LDAP stands for Lightweight Directory Access Protocol. As the name suggests, the original intention was to provide a simplified Directory Access Protocol (DAP). DAP is the subject of another series of international standards (known as X.500 (http://www.itu.int/ITU-T), which is also - with rather insignificant deviations - available as an ISO standard (http://www.iso.org; ISO/IEC 9594). Over the course of time, however, LDAP has evolved from a simple protocol to one that favors more X.500-like capabilities.
An LDAP directory contains entries. An entry is uniquely identified by its "Distinguished Name" (DN). DNs are structured hierarchically. Here are some examples of DNs:
-
c=BY (c normally stands for country, BY is a country name complying with ISO 3166 (http://www.iso.org))
-
o=composers, c=BY (o normally stands for organization)
-
cn=Igor Stravinsky, o=composers, c=BY (cn normally stands for common name)
-
cn=Marc Chagall, ou=modern painters, o=painters, c=BY (ou normally stands for organizational unit))
-
cn=Distribution List Sales, l=Thessaloniki (l normally stands for locality)
-
cn=Fedor Dostoevsky+fathersname=Mikhailovich, o=writers, c=BY
-
cn=Alexander Green, o=writers, c=BY
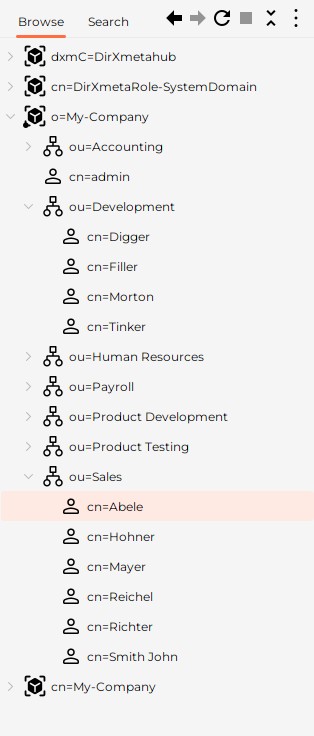
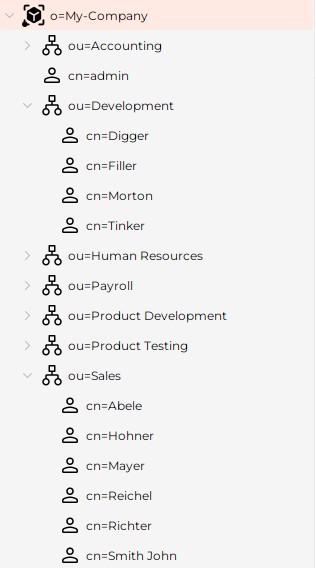
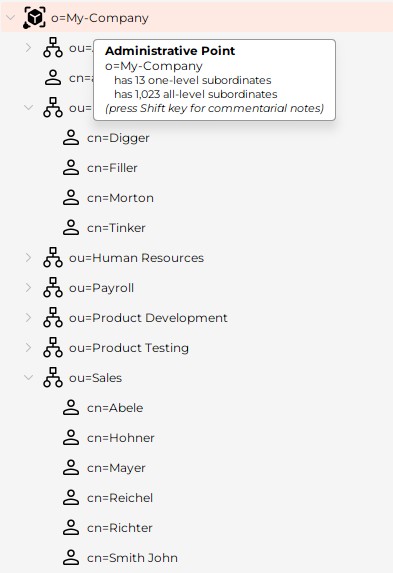
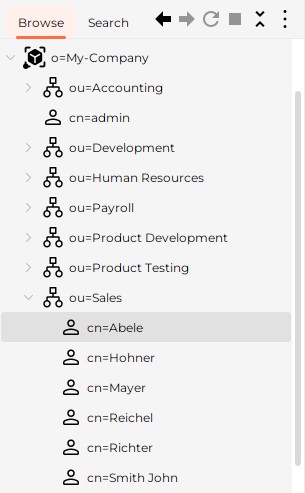
Here is a sample showing how as this application might present those entries in its so-called tree pane:
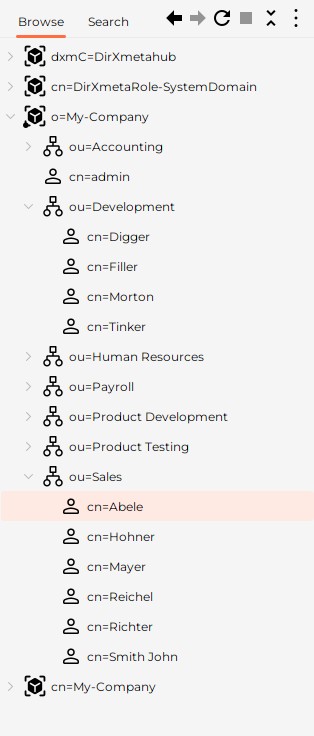
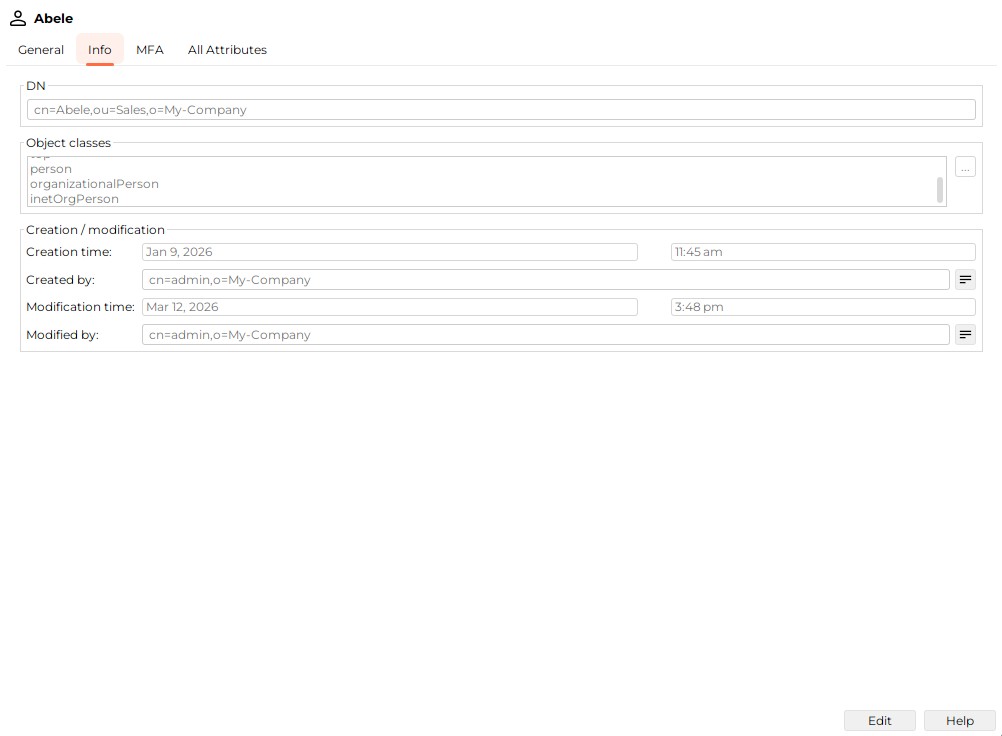
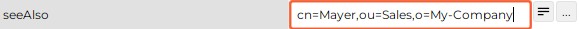
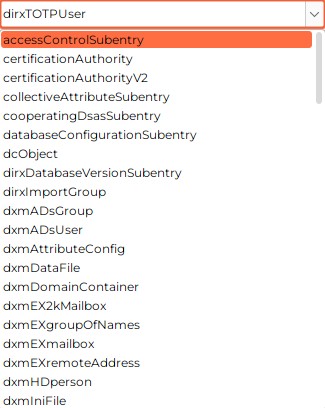
Entries are composed of a DN and a number of attributes. For example, an entry with DN cn=Abele,ou=Sales,o=My-Company might have the attributes:
-
objectClass:
-
dirxTOTPUser
-
top
-
person
-
organizationalPerson
-
inetOrgPerson
-
-
cn: Abele
-
sn: Abele
-
description: Sales Europe
-
telephoneNumber: +49(89)235-67543
DNs are composed of relative DNs (RDNs). For example, cn=Alexander Green, o=writers, c=BY is composed of three RDNs. RDNs must be derived from attributes. It is possible to compose an RDN of multiple attributes joined by “+” as in cn=Fedor Dostoevsky+fathersname=Mikhailovich,o=writers,c=BY. RDNs like this are called multiple naming attributes (or multiple attribute value assertion).
Since RDNs must be derived from attributes, the last RDN (Alexander Green in the previous example) is always available as an attribute of a given entry, too. As opposed to the last RDN however, the underlying attribute may be recurring. In the example used here, it has two values: "Alexander Green" and "Aliaksandr Gryneusky". One of them must be identical to the last RDN. "Alias" entries represent an exception to this rule: An Alias has only the two attributes objectClass and aliasedObjectName, but can use for its DN almost any sort of attribute but attributes with DN syntax.
The hierarchy starts from "Root" (commonly marked "/"). If you consult the previous examples, one level below "/", you will find "BY" and "Thessaloniki", one level below "BY" there is "composers", "painters" and "writers" and so on.
LDAP servers have at least one root node (also called a suffix or a context prefix), often unequal to "/" (o=painters, c=BY for example). LDAP servers only store their naming context; that is, their own root node and the entries that are subordinate to their root node. LDAP servers may be able to be configured to contact other servers automatically (chaining) or to return referrals that point to other servers when they are handling requests outside the scope of their suffix. This application can be configured to follow referrals (to some extent) or ignore them.
Attributes may be recurring, also called multivalued (like object class and cn in the previous example) or single-valued. Attributes have an attribute syntax. Here are some examples: Boolean, Country String, Certificate, DN, Directory String, Generalized Time, IA5, Integer, Jpeg, Numeric String, Postal Address, Telephone Number - and there are many more.
Attributes can be classified into
-
User Attributes
User attributes are all attributes except for operational attributes. -
Operational Attributes
Operational attributes are predefined attributes that are used for administrative purposes. For example, creatorsName is an operational attribute that stores the DN of the user who added the entry. -
Collective Attributes
Collective attributes are attributes that are common to multiple entries. These attributes are stored only once.
As specified by LDAP, entries must have a special recurring attribute that stores object classes (see the previous example). Object classes typically define the attributes that an object must have and may have. However, some LDAP servers allow you to switch off the "schema check" function. In this case, the object class is not much more than another possible search filter. Some LDAP servers do not use the object class recurring attribute at all.
There are several types of object classes:
-
Abstract Object Classes
Abstract object classes are used only to derive other object classes. Top is an abstract object class from which every structural object class is directly or indirectly derived (auxiliary object classes are usually derived from Top, too, but this is not mandatory). In many real world schemata, it is the only abstract object class you will encounter. -
Structural Object Classes
Each entry must have at least one structural object class. If an object class happens to be derived from of another object class, the affected entry has both object classes and inherits all attribute types from the parent object class. However, not counting "parent classes", each entry has one and only one structural object class. -
Auxiliary Object Classes
In addition to structural object classes, entries may have one or more auxiliary object classes. As opposed to structural object classes, auxiliary object classes can be added to and removed from an entry at any time. Auxiliary attributes are associated with a (possibly empty) set of attribute types. Auxiliary classes provide a convenient means to add attribute types (the ones that are associated with that auxiliary object class) dynamically to entries that are already defined by a structural object class. So, auxiliary object classes allow you to dynamically extend the permissible attribute set of entries beyond the one defined by their structural object classes. If the set of associated attribute types is empty, the auxiliary object class is an object class that at the same time is sort of an ordinary attribute. It may however serve as a filter for access control definitions in case the access control provided by the server follows the X.500 specification.
In the previous example, you can find the object classes top, person, organizationalPerson (usually derived from person), inetOrgPerson (usually either derived from organizationalPerson or an auxiliary object class).
LDAP provides several ways of searching:
-
Subtree search (an "all level" search)
Searches within the whole subtree rooted at the current entry.
If you refer to the previous example, a subtree search below c=BY with the search filter cn contains chag returns the entry cn=Marc Chagall, ou=modern painters, o=painters, c=BY as the search result. -
One level search
Searches among the "children" of the current entry (disregarding "grand children" and their "descendants"). If you refer to the previous example, a one-level search below c=BY with the search filter cn contains chag returns "successful" with the search result being empty. -
Base object search (a "zero level" search)
A base object search is not really a search. It can be used to read the current entry or to check for its existence.
Searches, particularly subtree searches, allow you to pass a more or less complex search filter in order to restrict the number of entries returned by the server. You may also pass a size limit and/or a time limit to save the server’s resources and to avoid slow reaction times and too many entries in the search result.
| LDAP servers usually use their own limits; LDAP clients cannot exceed these limits. |
What is returned as search result depends upon the conditions under which the software considers a value presented by a user to correctly match a value stored in the directory. This is where matching rules come into play. Matching rules are assigned to attribute types and must be compatible with the corresponding attribute syntax. A matching rule specifies how attribute values are to be matched for equality, ordering, or substring comparison. You cannot use attributes with no matching rule assigned (like fax in the examples to follow) in search filters.
Here are some examples of matching rules:
| Attribute | Matches for | |||
|---|---|---|---|---|
Type |
Syntax |
Equality |
Substring |
Ordering |
department |
DirectoryString |
Case-Ignore-Match |
Case-Ignore-Substring-Match |
— |
createTimeStamp |
GeneralizedTime |
Generalized-Time-Match |
— |
Generalized-Time-Ordering-Match |
jpegPhoto |
OctetString |
Octet-String-Match |
— |
— |
headCount |
Integer |
Integer-Match |
— |
Integer-Ordering-Match |
userCertificate |
Certificate |
Certificate-Exact-Match |
— |
— |
facsimileTelephoneNumber |
facsimileTelephoneNumber |
— |
— |
— |
There are many more possible matching rules.
What is returned in a search result also depends on the attributes that are requested to be returned:
-
Requesting All attributes means all user attributes of all entries matching the search filter are requested to be returned
-
Requesting All operational attributes means all operational attributes are requested to be returned.
This option is not necessarily recognized by all LDAP servers -
It is also possible to request exactly those attributes that are listed in a list of requested attributes passed with the search request. This is normally the most resource-saving way, since it avoids transferring unneeded data
Moreover, missing access rights (see below) may cause a search result to be incomplete.
At last, what is returned in a search result depends on the data that can be accessed: As mentioned above, a server does not necessarily store all the data itself. If not, in order to still be able to return complete search results, it relies on configuration provisions such as "Chaining" (i.e. the server "chains" to other servers, to get additional information) or "Referrals" (i.e. the server does not provide the complete search result itself, but leaves it to the client to complete it by providing referrals to it; the client may or may not "follow referrals").
Other - occasionally used - search options include:
-
"Types only"
You can have the search return only attribute types rather than types and values (which is the default). -
Dereference Aliases
Indicates how alias objects are to be handled in searching. The semantics of the possible values of this field are: -
neverDerefAliases (default)
Do not dereference aliases. -
derefInSearching
Dereference aliases in the search result. -
derefFindingBaseObj
The search base is de-referenced if it happens to be an alias. -
derefAlways
Dereference aliases both in the search result and in the search base.
Other requests specified in LDAP include:
-
Add entry
-
Modify entry
-
Rename entry
-
Delete entry
LDAP controls provide a mechanism for extending an LDAP operation. A control is a way to specify additional information as part of an LDAP request and an LDAP response.
A control specifies the following information:
-
A unique object identifier (OID), as defined by the creator of this control
The OID identifies the control. If you plan to use a control, you need to make sure that the server supports the control. Servers usually list all or some of the controls they support in the supportedControl attribute in the root DSE. You can acquire the root DSE by doing a search where the scope is "Base", the base DN is "" (empty string) and the search filter is (objectclass=*). Alternatively, you can have tools like DirX Directory Manager display the root DSE including its supportedControl attribute. -
An indication of whether the control is critical to the operation
-
Optional data related to the control (for example, for the server-side sorting control, the attribute to be used for sorting search results)
If an LDAP request contains a control, the server may respond in one of the following ways:
-
If the server supports this control and if the control is appropriate to the operation, the server should make use of the control when performing the operation
-
If the server does not support the control type or if the control is not appropriate, the server is supposed to do one of the following:
-
If the control is marked as critical to the operation, the server should not perform the operation and should instead return the result code "Unavailable critical extension".
-
If the control is marked as not critical to the operation, the server should ignore the control and should perform the operation.
Servers can react to some sorts of controls by sending controls back to clients. Example: "Server Side Sorting" is provoked through the "Server Side Sorting Request Control", which specifies details such as the attribute type to use for sorting. The server is to send back a "Server Side Sorting Response Control", which tells whether the result is sorted or not - and if not why not.
This application inspects the LDAP Root subentry to find out what controls the server supports and implicitly makes use of all or some of the available controls. Details are available in the section "LDAP Root Subentry" (provided the DirX Directory Manager plug-in is installed).
The LDAP server may refuse to handle a request because of missing access rights. Access rights depend on the user’s authentication. A user authenticates himself through a bind (called login in this application). The default bind "Anonymous" is implied. The LDAP server usually configures an anonymous bind to permit read access for anyone to a well-defined subset of the data stored in the server’s database. More comprehensive access rights typically require a DN and a password to be passed (basic authentication). Particularly for access from the Internet or an extranet, it might be a good idea to use secure authentication by combining basic authentication with SSL (secure socket layer) or its designated successor TLS (transport layer security).
| LDAP server does not necessarily reveal the fact that it did not handle a particular request due to missing access rights. Instead, it might return an error code like "not found", for instance. |
The hierarchical structure of the DN suggests that you consider the directory to be a tree. Also, the tree-like collection of all DNs that comprise a particular, possibly distributed directory is called the Directory Information Tree (DIT). This is justified to some extent; however, alias entries allow the tree structure to be circumvented.
Available LDAP Functions
Unless disabled, the core component typically makes its LDAP functionality available in one or more view groups which you can access through:
-
The application menu
-
The node toolbar
-
The right mouse button
These functions include:
-
Browsing the LDAP directory tree
-
Creating new LDAP directory entries
-
Deleting LDAP directory entries
-
Exporting/Importing LDAP directory entries
-
Displaying administrative information on the server (the so-called LDAP root DSE, where "DSE" stands for directory-specific entry)
-
Logging in/out to/from an LDAP directory
-
Moving LDAP directory entries to a different parent
-
Copying LDAP directory entries
-
Showing and modifying properties of LDAP directory entries
Some rather uncommon properties (like MHS OR address) are not or not fully supported. -
Changing passwords (your own password as well as somebody else’s password)
-
Renaming LDAP directory entries
-
Searching the LDAP directory by specifying simple or complex search conditions
(see the Search pane and search dialog topics) -
Abandoning an in-process, but uncompleted search operation.
In order to be able to access an LDAP directory, you must provide some information like the address and port number (default: 389) of the LDAP directory server. This information may already be pre-configured, but you may also be able to edit this information by right-clicking on the top node of a tree and selecting "Server". Alternatively, you may find this functionality in the menu.
Additional administrative functionality (e.g. schema management) may be available in addition to the functionality the core component provides, depending on what plug-ins are installed.
The core component’s LDAP access functionality can be generic or customized.
-
Generic LDAP access means that the core component has no built-in knowledge about the LDAP directories to be accessed. If the core component is unable to retrieve the schema from an LDAP server, the functionality that is based on the knowledge of schema information - like objects classes and attributes - is unavailable unless the missing information is supplied in the application’s configuration files. In particular, searching may become unusable.
-
Customized LDAP access means that the core component has pre-configured information about the objects and attributes of one or more LDAP directories to be accessed.
LDAP directories are organized in a tree-like manner. This organization may or may not be visible in a particular view.
SSL/TLS
SSL stands for Secure Socket Layer. It is a common technique to have TCP/IP network communication encrypted based on "trusted" certificates. TLS stands for Transport Layer Security; it is a not overly significant, evolutionary advancement over SSL and has de facto replaced SSL. What is used in a particular connection (TLS or SSL) is the result of a negotiation between client and server. Possibly more important, the key length is negotiated, too.
There are two security stages:
-
Stage 1 ("certificate-based server authentication"): if you want to make sure the server you are talking to is actually the one you think it is. This application supports Stage 1.
Stage 1 implies encryption -
Stage 2 ("certificate-based client authentication"): if the server asks you to authenticate yourself through a certificate.
In order to get SSL/TLS working, you must
-
Ensure the server supports it and is configured appropriately
-
Ensure that a suitable certificate is available in your local "keystore". By "suitable", we mean that the certificate transmitted by the LDAP server must be trusted by at least one of the certificates stored in the keystore that is assigned in the function "Options" (menu "Tool"). Note that
-
This application ships with a keystore file called cacerts that contains a demonstration certificate that is aligned with the demonstration certificate DirX Directory brings along. With this demonstration certificate you are able to run SSL/TLS out-of-the-box in conjunction with DirX Directory by way of trial.
-
The Java Runtime Environment, too, ships with a keystore (also a file called "cacerts") containing a number of root Certificate Authority (CA) certificates in its keystore.
-
You can assign only one keystore for all secure connections within this application, i.e. it is not possible to assign one keystore for server A and another one for server B. Choosing a different keystore requires this application to be exited and started again to get the new keystore effective.
-
The function "Options" allows for managing keystores. Alternatively, you can use the keytool command that ships with the Java Runtime Environment. If your certificate is stored in a file called, for example, myCA.der, and you want to know it from other certificates stored in the same keystore by the name myName and if your keystore resides in, for example, C:\jre\lib\security\cacerts, you use it like this:
keytool -import -file myCA.der -keystore C:\jre\lib\security\cacerts -alias myName
You will be asked for a password. The default password for the keystore shipping with this application is "dirx". The default password for the keystore shipping with Oracle’s JRE is "changeit".
You may find the command keytool -help useful, too.
For more detailed information on the keytool command, please refer to the URL given at the beginning of this topic. -
Activate SSL/TLS in this application.
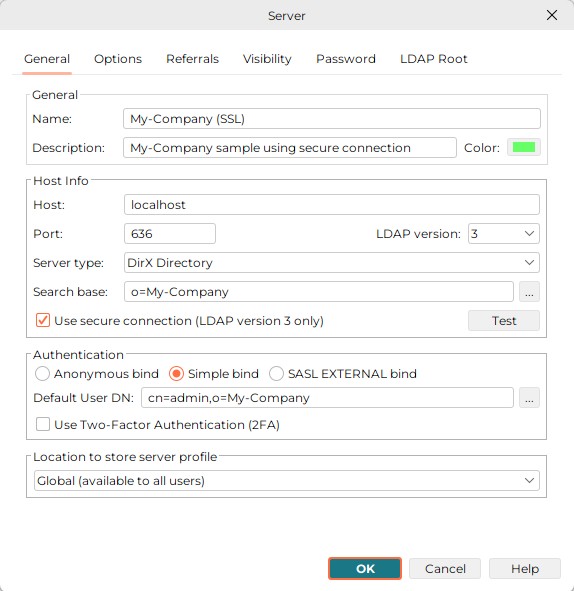
The default port for secure connections is 636. To activate SSL/TLS (more exactly, certificate-based server authentication), check "Use secure connection (LDAP version 3 only)" in the Server dialog as shown in the following example of the server dialog. This checkbox is not available if the Java Runtime Environment you are using does not support SSL/TLS.
Here is an example:
Smart Card Login
From the LDAPv3 protocol view Smart Card Login (SCL) maps onto an LDAP SASL bind with the mechanism type EXTERNAL. This means the security services of the underlying TLS/SSL layer is used to perform the client authentication that is based on strong cryptography.
After a successful bind the DSA determines the Authorization Identity of the user. This is the basis for the Access Control decisions made in all subsequent operations. By default, the Authorization Identity is mapped to the DN specified in the subjectDN from the user’s certificate.
The following sections describe how to set up Smart Card login with DirX Directory Manager.
Software Requirements
SCL requires that the software product Eviden CardOS API (64-bit) is installed. After a successful default installation of CardOS API the PKCS#11 library named "cardos11_64.dll" is in the folder
-
C:\Windows\System32
Configuring the PKCS#11 Library for DirX Directory Manager
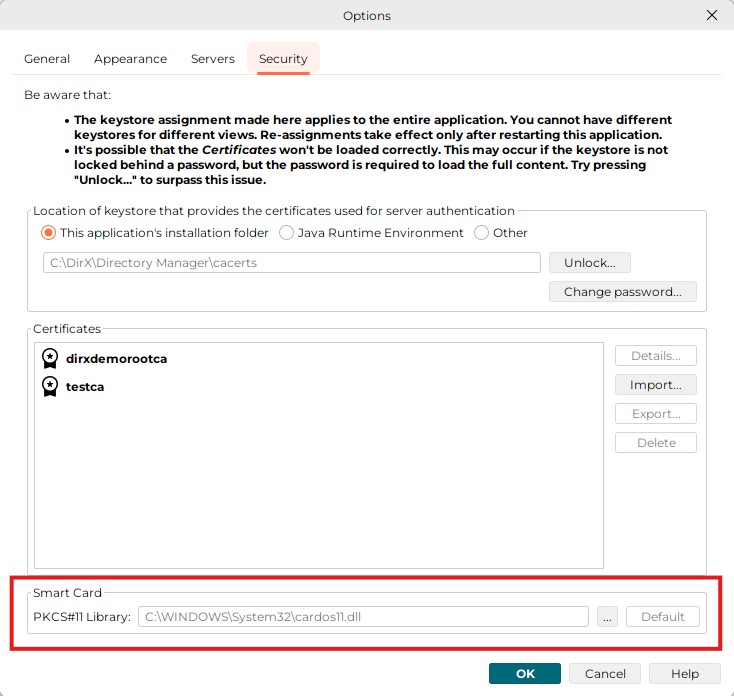
In order to successfully perform SCL logins, the path to the PKCS#11 library cardos11.dll must be specified in DirX Directory Manager. In Application menu → Options → Security, specify the path in the Smart Card section:
Setting up the LDAP Server and the DSA for Smart Card Login
In order to successfully perform a sasl EXTERNAL bind the LDAP server must meet the following preconditions additionally to those that are required for SSL binds without client authentication:
-
The LDAP server must request from the client to perform client authentication when SSL/TLS is used. This behavior is specified in the LDAP SSL Client Authentication Required attribute.
-
The value of the LDAP SASL Authz Id Mapping (LSAIM, ldapSaslAuthzIdMapping) must specify how the DSA determines the requestor used for all operations following the bind. The default is Use subjectDN from Certificate as the bind initiator.
-
The LDAP server must trust the CA that issued the clients userCertificates; that is the CA certificate must be added to the LDAP Trusted CA Certs (LSTCC, ldapTrustedCACerts) attribute.
-
Depending on the value of the LDAP SASL Authz Id Mapping attribute an INITIAL index must be created for the attribute that the mapping is based on.
-
The SSL-External-DAP bind between the LDAP server and the DSA that the ldap sasl bind is mapped upon must be a local one, that is the LDAP server and DSA must run on the same host. Otherwise, the environment variable DIRX_SSL_HOSTS can be used to specify the IP address that the DSA accepts as initiator hosts for LDAP SASL bind with the mechanism type EXTERNAL.
Perform the following steps to prepare the LDAP server and the DSA for Smart Card login:
Configuring the LDAP Server:
-
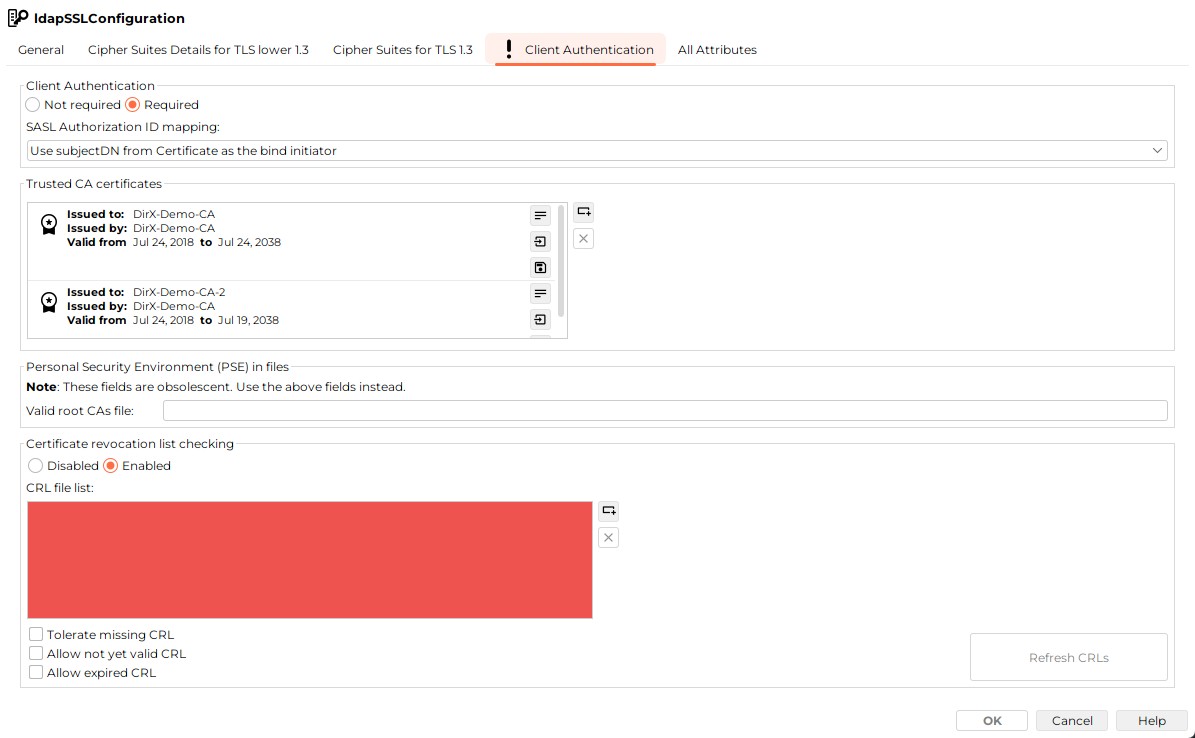
In the Configuration View, edit the LDAP SSL configuration subentry to specify the values for the attributes:
-
LDAP SSL Client Authentication Required
-
LDAP SASL Authentication ID Mapping
-
LDAP Trusted CA Certs
-
In the Client Authentication tab, check Client Authentication Required to set the LDAP SSL Client Authentication Required (LSCAR, requireSSLClientAuth) attribute to TRUE. The LDAP server now requests from the client to perform client authentication when SSL/TLS is used.
-
The value of the LDAP SASL Authentication ID Mapping attribute is managed together with the Client Authentication. In our example the DSA uses the subject name of the userCertificate that the client provides in the context of the sasl bind operation. So leave the value Use subjectDN from Certificate as the bind initiator for SASL Authorization ID mapping unchanged.
-
Finally add the CA certificate to the LDAP Trusted CA Certs (LSTCC, ldapTrustedCACerts) attribute that the LDAP server trusts the CA that issued the clients userCertificates. In the Client Authentication tab → Trusted CA certificates section, press Adds a new item (Insert) button to open file selection dialog. Select the CA certificate file and press the Import button to add the CA certificate to the list of trusted CA certificates.
The following figure illustrates the relevant settings of the LDAP SSL Configuration subentry:
Configuring the DSA:
-
Recall from the settings of the LDAP SSL configuration subentry that the LDAP SASL Authz Id Mapping attribute specifies how the DSA determines the DN of the bind requestor from the sasl bind credentials:
-
For the default Use SubjectDN from Certificate of the bind requestor no additional index is necessary.
-
For Use the directory entry that owns the Certificate as bind initiator an initial index for the userCertificate Attribute is required.
-
For Use the directory entry that owns the email attribute of the Certificate Extension altName as bind initiator an initial index for the email Attribute is required.
In our example it is not necessary to create an additional index because the default value is used.
-
If the LDAP server and the DSA are not colocated add the IP address to the environment variable DIRX_SSL_HOSTS. (See "Environment Variables" in the DirX Directory Administration Reference for details.)
Now the DSA and the LDAP server are prepared to accept LDAP SASL binds with the mechanism type EXTERNAL.
Setting up the Client
From the LDAP client perspective SCL is one flavor of SASL EXTERNAL binds. In the General tab of the Server properties → Authentication check SASL EXTERNAL bind and select Smart Card (PKCS#11) for Client Keystore:
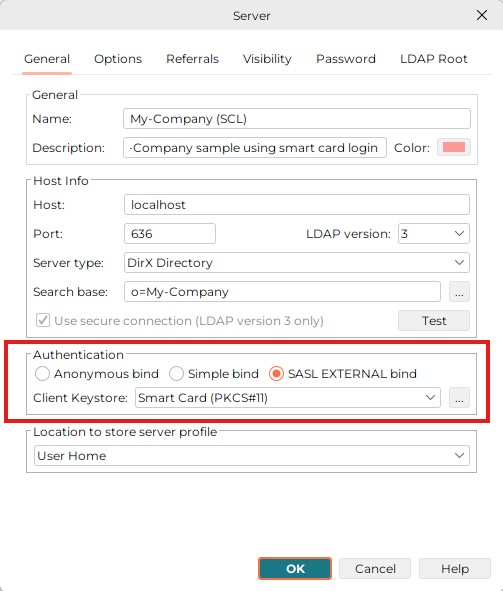
Now DirX Directory Manager and the DirX Directory service are prepared to accept smart card logins.
See the Release Notes for information about supported smart card types.
Basic Patterns/LDAP Functionality
The following chapters provide information on the basic patterns supplied by the core component of this application. They also cover the "core" LDAP functionality that forms an integral part of the core component.
| Some advanced LDAP features like schema management or subentry management are not supplied by the core component; they are only available, if the corresponding plug-ins are installed. |
The following sections cover the core component’s basic patterns and LDAP functionality:
-
Special Mouse Operations
-
Positioning
-
Abandoning an in Process Search
-
View Panes
-
Property Editors
-
Standard Dialogs
Main Window
The main window is a frame around the different views. It consists of a Logo Panel a Title Panel, an Outlook Panel, a Tree Panel and a Work Area.
Logo Panel
The logo panel is located in the top left corner of the main window, above the Outlook panel. It displays the application logo by default.
In its bottom-right corner, there is a  button, which lets you expand or collapse the Outlook panel.
button, which lets you expand or collapse the Outlook panel.

| You can customize the logo panel to display your own logo. For details, see Logos. |
Title Panel
The title panel at the top of the main window displays the name of the currently selected view on its left-hand side. On the right-hand side, it displays the DN of the currently logged-in user and label with hostname:port of the connected LDAP server. Hover the mouse pointer over the hostname:port label to see more information.
| The hostname:port label changes color based on the color which was assigned to the connected LDAP server profile. |
On the right-hand side of the title panel, there is a Application Menu button that provides quick access to personal settings and functions. The icon of this menu shows a warning sign if the connection secure (SSL is not used).
Application Menu
Click the Application Menu button to open it. It contains the following entries:
-
Trace Output… - Opens the Trace Output dialog, which displays the trace output of this application.
-
SNMP Trap Viewer… - Opens the SNMP Viewer dialog, which displays SNMP traps received by this application.
-
Close Server - Closes the connection to the currently displayed server. This entry is only available if a connection to a server is currently open.
-
Options… - Opens the Options dialog. See Customizing in the Options for details.
-
Help… - Opens the documentation at default page in chosen web browser.
-
Contextual Help - After clicking this entry, you can click most items in the current view to get help information about it.
-
About… - Opens the About DirX Directory Manager dialog. Contains info about the version of the core component ("Framework"), versions of the installed plug-ins and the version of the Java Runtime Environment (JRE) that started this application. Additional data that is primarily used for maintenance purposes. Plug-ins may extend the "About" dialog.
-
Exit - Closes DirX Directory Manager
This application will try to present itself at the next start-up just the way it appeared at the time you exited it. For this reason, it tries to store related information on disk or in the directory before finally exiting.
Outlook Panel
DirX Directory Manager provides the following view groups displayed in the Outlook panel on the left-hand side of the main window as part of its core:
-
Directory Entries
-
Quick Search
Other view groups may be available, depending on the server type and plug-ins installed.
Tree Panel
The tree panel is located on the left half of the main window, right of the Outlook panel. It displays a hierarchical tree of objects that you can select to view or edit in the work area. It has a minimum width set but can be resized by dragging the splitter bar that separates it from the work area.
Node Toolbar (and Menu)
This component takes its name from the nodes of the tree (objects) as they are the primary targets of the actions here.
It contains these actions:
-
 Back (Alt+Left arrow) - There is a tracked list of the objects you have selected in the tree in order. Pressing this button traverses this list to its beginning, selecting the objects in the tree. When you get to the first object, it becomes disabled.
Back (Alt+Left arrow) - There is a tracked list of the objects you have selected in the tree in order. Pressing this button traverses this list to its beginning, selecting the objects in the tree. When you get to the first object, it becomes disabled. -
 Forward (Alt+Right arrow) - There is a tracked list of the objects you have selected in the tree in order. Pressing this button traverses this list to its end, selecting the objects in the tree. When you get to the last object, it becomes disabled.
Forward (Alt+Right arrow) - There is a tracked list of the objects you have selected in the tree in order. Pressing this button traverses this list to its end, selecting the objects in the tree. When you get to the last object, it becomes disabled. -
 Refresh (F5) - Refreshes the data in the tree and work area, usually from the directory service.
Refresh (F5) - Refreshes the data in the tree and work area, usually from the directory service. -
 Stop - Stops the currently running operation. Disabled if no operation is running.
Stop - Stops the currently running operation. Disabled if no operation is running. -
 Collapse All - Collapses all nodes, keeping only root visible.
Collapse All - Collapses all nodes, keeping only root visible. -
 Node Menu - Opens the menu with more actions
Node Menu - Opens the menu with more actions
Extra actions in the Node Menu:
Export…
Allows you to export data from the LDAP server that is currently addressed into a file.
Export files can be:
-
LDIF content files (http://www.ietf.org/rfc/rfc2849.txt)
-
DSML v1 files (http://www.oasis-open.org/)
Values only containing ordinary ASCII letters (with minor exceptions) are exported as is, while others get base64 encoded. Exception: In case of DSML v1, DNs are always exported in "native" UTF-8. Base64 (see also RFC 2045) regulates how to transform binary data into printable data using nothing but the 64 characters "A-Z, a-z, 0-9, +, /". Base64 increases the original size by 33%; it is not an encryption.
Notes
-
The export of collective attributes is to be taken with a grain of salt, since it is impossible to find out beyond all doubt whether an attribute is collective or not. So, as a substitute, all attributes whose type starts with "collective", are taken as collective attributes.
-
Access Control may keep you from getting certain entries or certain attribute values.
-
Administrative restrictions configured at the LDAP server may cause the export function to terminate uncompleted.
The advance button offers additional options.
Import…
Allows you to import data from a file into the LDAP server that is currently addressed.
Import files can be:
-
LDIF change files (http://www.ietf.org/rfc/rfc2849.txt)
-
LDIF content files (http://www.ietf.org/rfc/rfc2849.txt)
-
DSML v1 files (http://www.oasis-open.org/)
-
DSML v2 files (http://www.oasis-open.org/)
As for the character encoding, the same regulations as with export apply; additionally, "native" UTF-8 is recognized for attributes, too.
+
The advance button offers additional options.
+ See also:
-
Exporting/importing certificates
-
Exporting/importing JPEG images
Actions present with DirX Directory server: * Import Schema… - * Export Schema… - * Compare Schemata… - * Open Schema File… -
Work Area
The largest part of the Main Window. Its content is based on the selected View and Node.
Actions
Cut/Copy/Paste
Allows you to use typical clipboard functions on currently selected entries. Works in list panes and tree panes (crosswise, too). Works also between different instances of this application.
See also: Drag&Drop.
Delete Entry
Allows you to perform standard "delete" functions:
-
Deletes the entry/entries currently selected
-
Checking off the "with all children" check button will cause all children to be deleted, too (recursively)
| A delete operation may fail due to the existence of administrative children that are invisible to the client |
Rename
Allows you to rename the object that is currently selected.
Notice the special LDAP feature "Retain old name". It allows you to let the old name survive in the attribute that stores the last RDN. For the DN itself, however, only the new name counts. Repeated execution of the rename function with "Retain old name" checked leads to a number of values in that attribute.
For details refer to the description of the "Standard Dialog" Renaming
Customizing in the Options
You can open the Options dialog from the Application Menu. It contains these tabs:
General Tab
The General tab allows you to customize the following settings:
-
Help
-
Help location - you can choose between Online Help and Offline Help. The Online help is available at public URL and is updated with every release. The Offline help is the one that is included in the installation package and is available without internet connection - but it is only relevant for the release you have installed and will not be updated.
-
Web browser - Select the web browser used to open web pages. You can choose from the installed browsers found by the application. If no installed browsers are found, error will appear when opening help.
-
-
Tooltips: Enable or disable tooltips in the application.
Appearance Tab
The Appearance tab allows you to select between the default Themes. Application must be restarted for the changes to take effect.
To customize the appearance further, see Customizing the Look and Feel.
Servers Tab
The Servers tab allow you to customize the following settings:
-
Views
-
Show confirmation dialog when closing a server - If enabled, a confirmation dialog will appear when you try to close a server connection. This can help prevent accidental closure of server connections.
-
Security Tab
The Security tab allows you to customize the following settings:
-
Select the location of keystore for server authentication. Use Unlock… to open the keystore and enter the password. You can also change the password by clicking Change Password….
-
Manage the Certificates.
-
Select the location of PKCS#11 Library for hardware token support (Smart Card).
| By specifying a keystore that doesn’t yet exist, you can cause an empty keystore to be created. |
Special Mouse Operations
Some functionality is available through special mouse operations:
-
Drag & Drop
-
Tooltips
-
Right Mouse button
-
In tree and list panes
-
In text fields
-
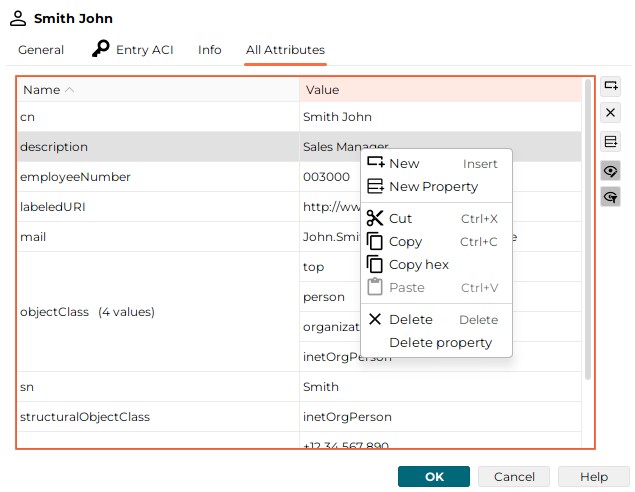
In the All Attributes Tab of property dialogs/panes
-
In the column headers of list panes
Drag&Drop
Drag and drop allows you to copy or move currently selected entries to different nodes. Drag and drop works in list panes and tree panes (crosswise, too); and it works also between different instances of this application.
See also: Clipboard functions in the Edit menu and in the property pane/dialog.
Tool Tips
This application makes extensive use of tool tips. Tool tips are contextual annotations that are briefly displayed when the mouse cursor remains on a context-sensitive spot, for example, on a property value.
Right Mouse Button
The places where the right mouse button is functional include
-
Tree and list panes
-
Text fields
-
The All Attributes Tab of property dialogs/panes
-
The column headers of list panes
Tree & List Panes
Some menu items are additionally available through the right mouse button.
Some functions are solely available through the right mouse button:
Plug-ins can add menu items to the right mouse button and modify right mouse button menu items.
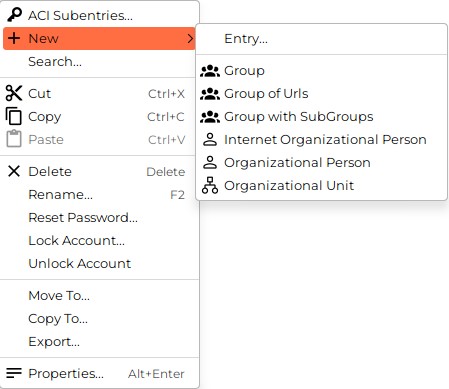
Here is an example of the right mouse button selection (right-clicking the mouse on an entry):
ACI Subentries
This operation is only available with DirX Directory V9.1 and later. It is the extended operation dsa_relevant_aci (OID 1.3.12.2.1107.1.3.2.13.52).
|
Opens a dialog that displays the ACI subentries relevant to the currently selected entry:
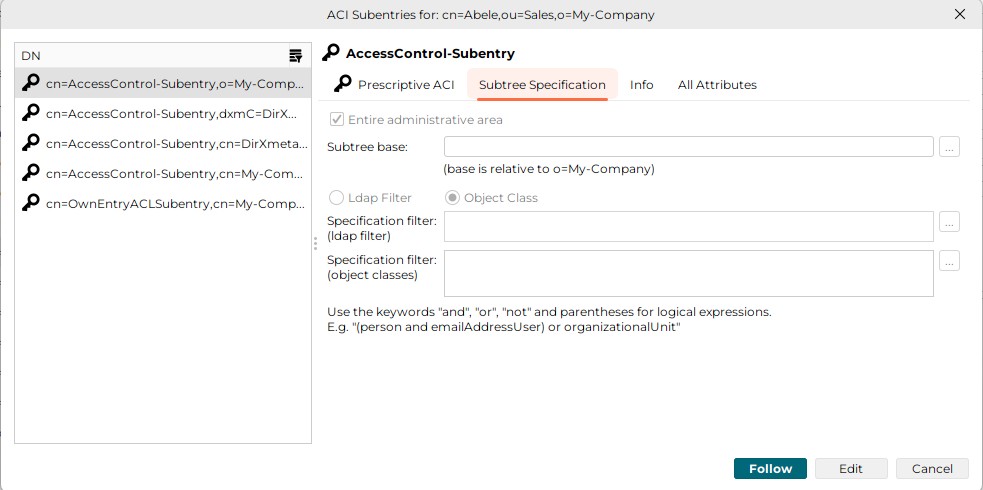
On the left-hand side, there is a list of the DNs of the ACI subentries relevant to the currently selected entry. On the right-hand side, the properties of the selected ACI subentry are displayed in a property pane. The dialog provides these buttons:
-
Follow - Follows to the selected ACI subentry in the tree and work area, closing the dialog.
-
Edit - Allows to edit the selected ACI subentry directly in the dialog. The changes are saved to the server when you press the Save button.
-
Cancel - Closes the dialog.
Copy To
Copies a node including all its children to a different parent.
| If the LDAP server does not support simple paging, restrictions like time/size limit may keep this operation from completing. |
Move To
Moves a node including all its children to a different parent.
| Not all LDAP servers support this feature. |
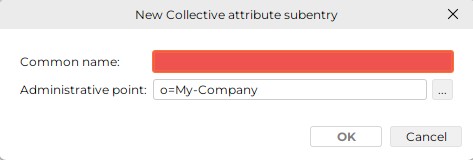
New
Creates a new entry in the server currently addressed below the node to which the right mouse button has been applied.
| This operation may fail for several reasons, for example: |
-
You do not have the required access rights.
-
The LDAP server is configured so that it does not permit you to create a DN like the one you have chosen.
Usually, the function offers a limited selection of possible types of objects:
-
(Generic) Entry
-
Group
-
Group of URLs
-
Group with SubGroups
-
Internet Organizational Person
-
Organizational Person
-
Organizational Unit
Depending on the number of possible types of objects, the core component provides four variants (which plug-ins may or may not use).
(Generic) Entry
If the type of object is not pre-specified, you must first complete a dialog like this:
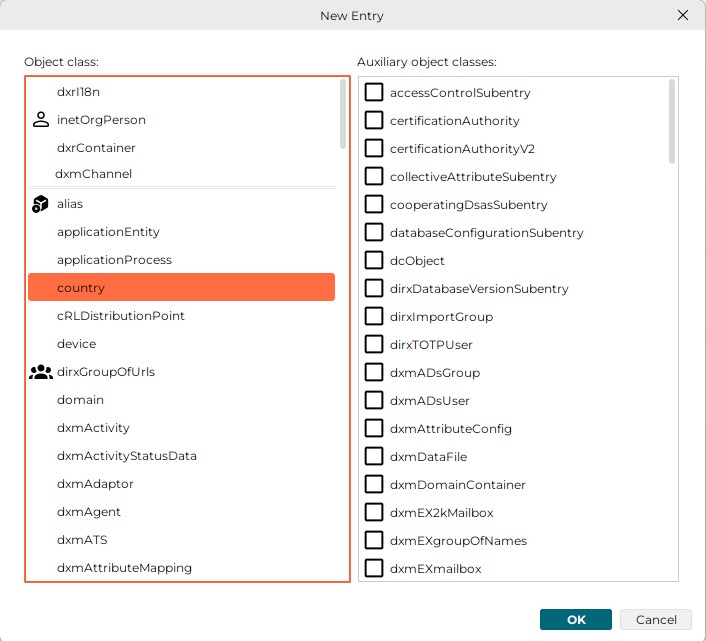
It allows you to specify (based on information provided by the server):
-
One structural object class and (left half of dialog)
-
A number of auxiliary object classes (right half of dialog)
| The last recently used structural object classes are repeated in the upper part above double line. |
After you complete this dialog, you can complete the creation of the entry in a dialog like this:
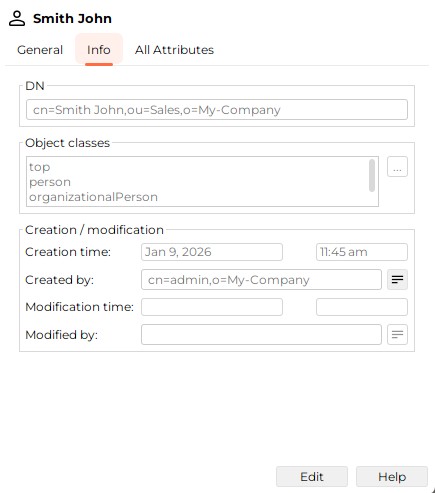
Tab: Info:
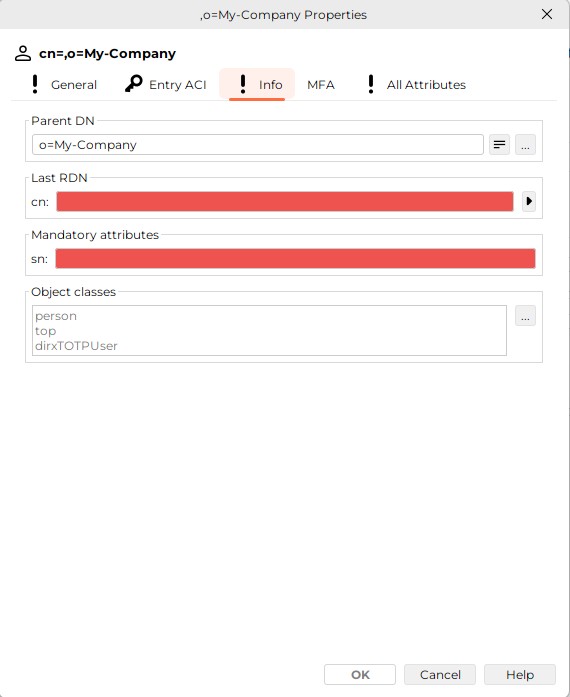
This tab displays
-
The Parent DN (read-only)
-
The last RDN (red shadowed)
-
All additional mandatory attributes (red-shadowed; there are no additional mandatory attributes in the screenshot above)
-
All Object Classes (read-only)
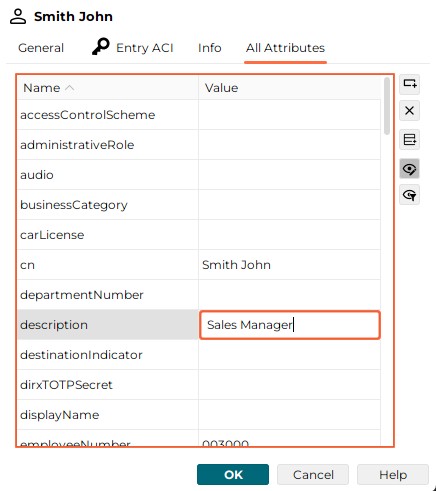
Tab All Attributes:
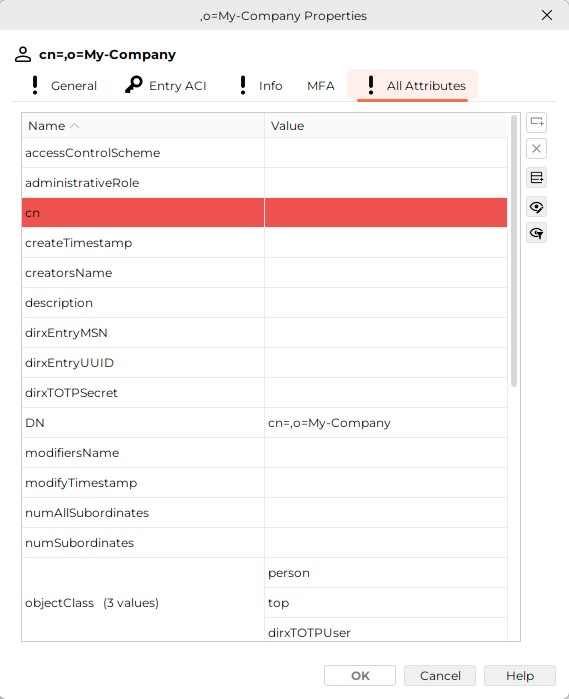
This tab displays all attributes. The mandatory ones are highlighted in red.
You can assign multiple naming attributes, too. For details refer to "Renaming".
Group
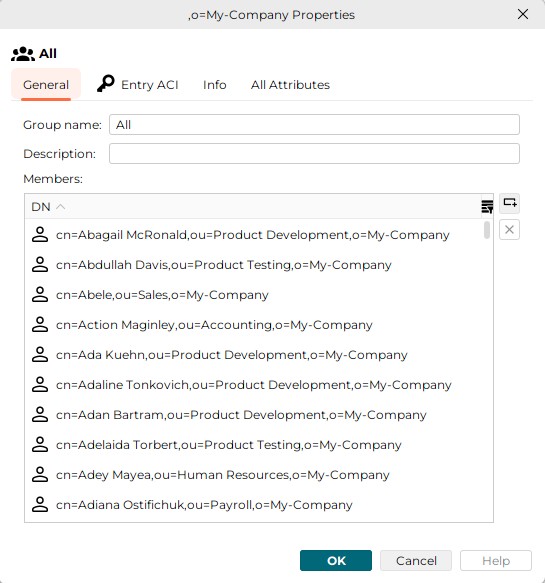
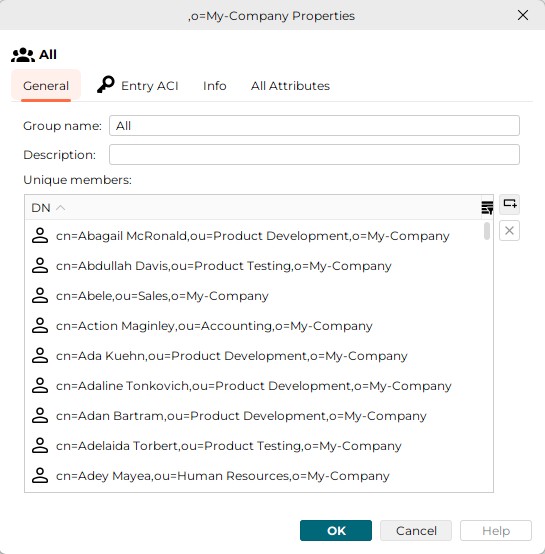
If the object class "Group" is pre-configured, the dialog should look like this:
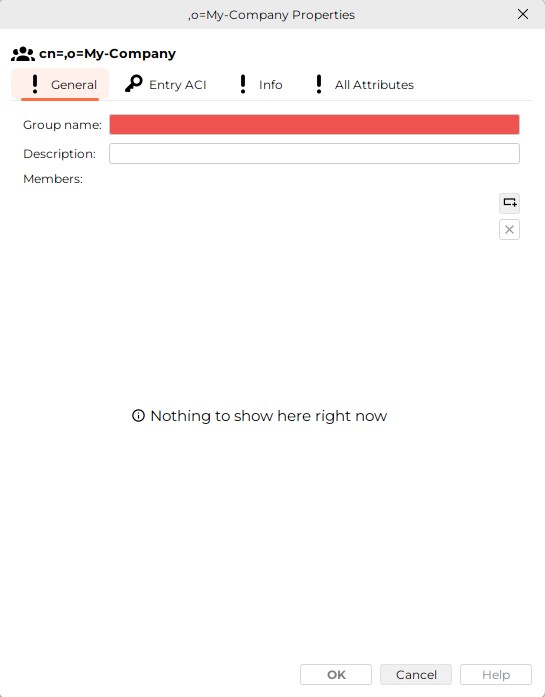
The Members list appears when at least one member is added.
The "Info" and "All Attributes" tabs have the same meanings as the Info and All Attributes tabs of the "Entry" dialog.
Group of URLs
If the object class "Group of URLs" is pre-configured, the dialog should look like this:
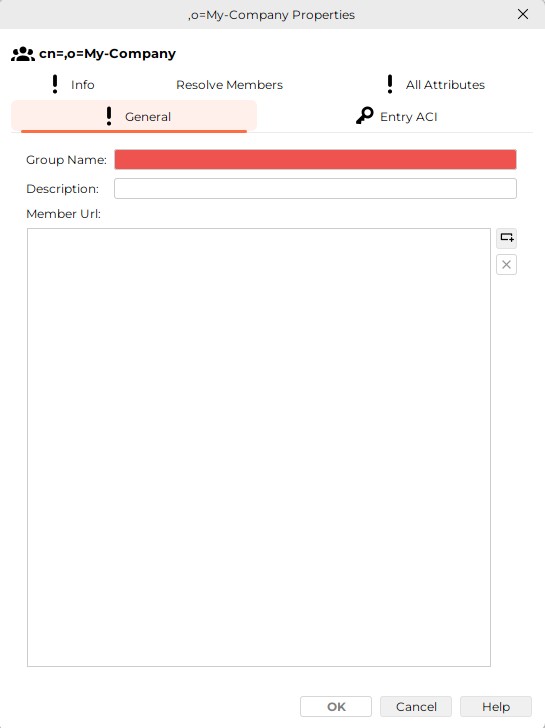
The "Info" and "All Attributes" tabs have the same meanings as the Info and All Attributes tabs of the "Entry" dialog.
Group with SubGroups
If the object class "Group with SubGroups" is pre-configured, the dialog should look like this:
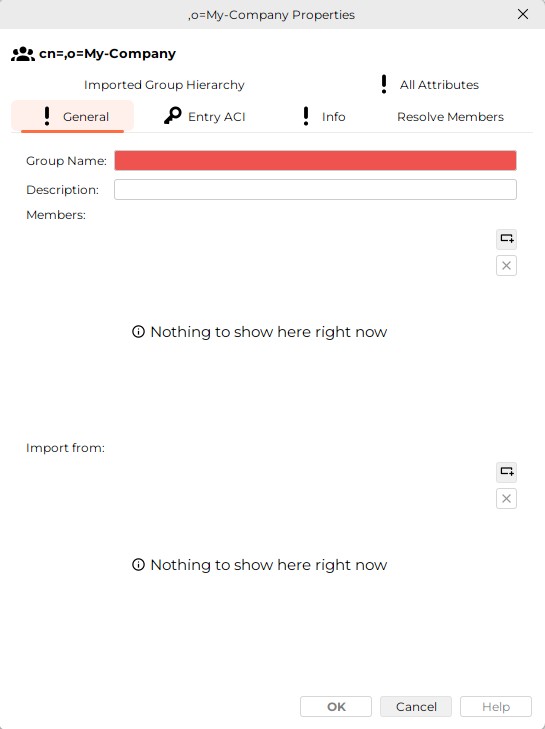
The Members list appears when at least one member is added. The Import from list appears when at least one subgroup is added.
The "Info" and "All Attributes" tabs have the same meanings as the Info and All Attributes tabs of the "Entry" dialog.
Internet Organizational Person
If the object class "Internet Organizational Person" is pre-configured, the dialog should look like this:
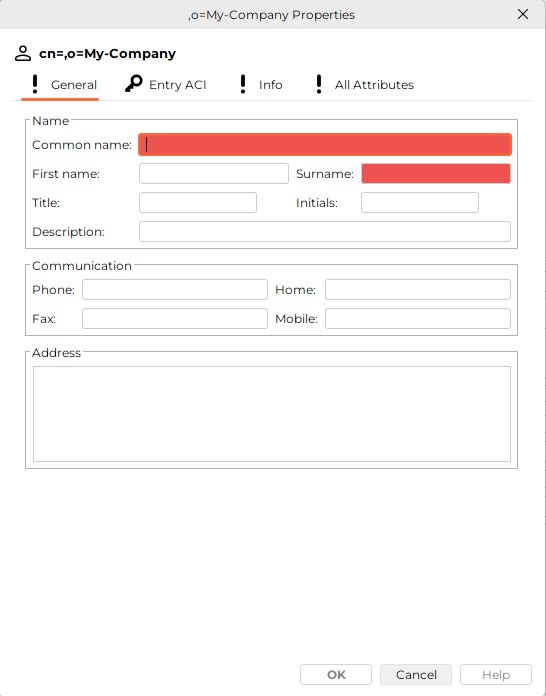
The "Info" and "All Attributes" tabs have the same meanings as the Info and All Attributes tabs of the "Entry" dialog.
Organizational Person
If the object class "Organizational Person" is pre-configured, the dialog should look like this:
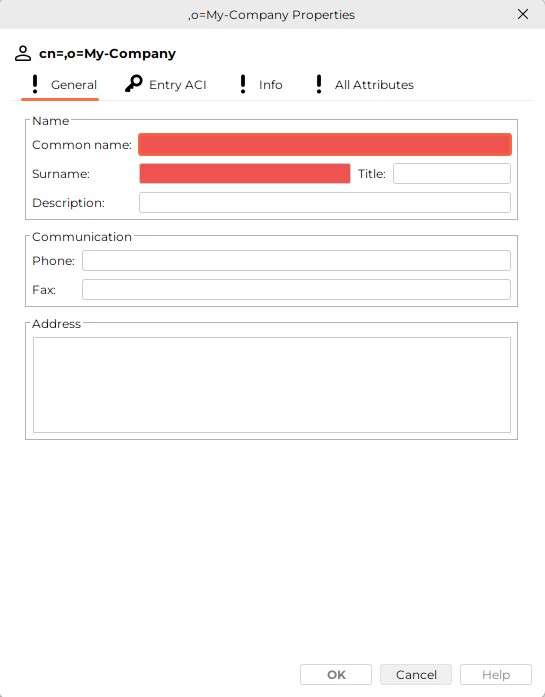
The "Info" and "All Attributes" tabs have the same meanings as the Info and All Attributes tabs of the "Entry" dialog.
Organizational Unit
If the object class "Organizational Unit" is pre-configured, the dialog should look like this:
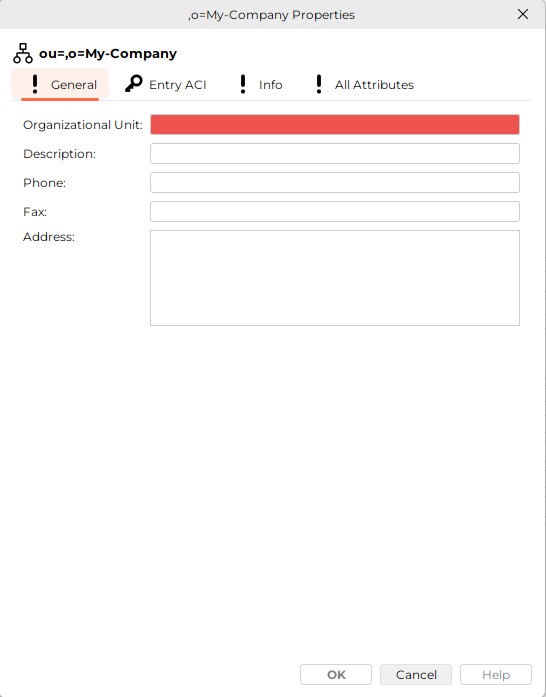
The "Info" and "All Attributes" tabs have the same meanings as the Info and All Attributes tabs of the "Entry" dialog.
Variants
Depending on the number of possible types of objects, the core component provides these variants (which plug-ins may or may not use):
-
Objects of only one type can be created below the current node.
-
A limited selection of object types can be created.
Here is an example (only these types of objects can be created):
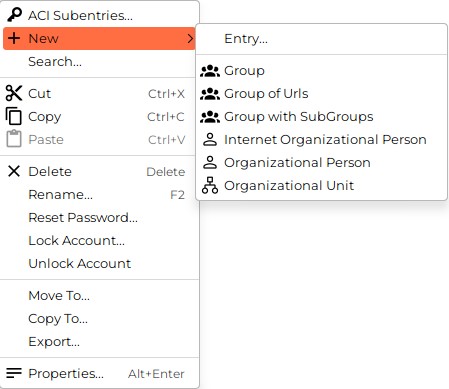
-
A large selection of object types can be created.
-
The type of the new object can be entered via the keyboard.
Lock/Unlock Account
Allows to prevent logins with the distinguished name (DN) of the currently selected entry or - if the entry is locked out already - to re-admit logins with that DN. Note that the server may lockout the DN as well implicitly, e.g. after a configured number of incorrect logins.
Here is an example of the context menu:
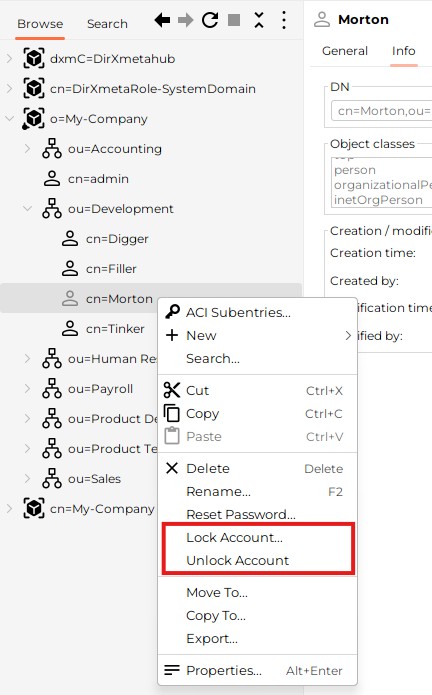
In this example, the entry cn=Morton is marked locked out by greyed-out icon. Note that in a network being comprised of several DSAs (supplier and consumers) the entry might be locked or marked locked at some DSA(s) other than the one, this application is currently bound to.
| An entry being locked out at some different DSA(s) only is not visualized through the greyed-out icon! |
The context menu provides two items of interest here: Lock Account… and Unlock Account….
-
Both items are grayed out and not selectable, if the server does not appear to support this functionality (more precisely: if the operational attribute pwdAccountLockedTime is missing in the schema).
-
Unlock Account… is offered even if the entry appears to be unlocked anyway, since it cannot be excluded that the entry is locked out at some other DSA(s) (see above). The chaining and shadowing mechanisms of DirX Directory are supposed to propagate the unlock operation to all participating DSAs, particularly to the ones that are affected (if any).
-
Lock Account…
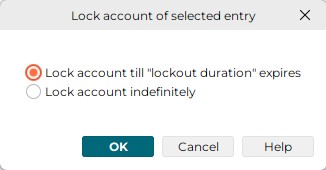
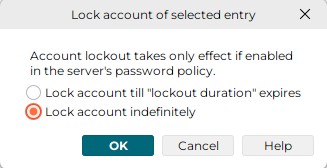
You can lock an account indefinitely, or you can lock it till the "lockout duration" expires. The lockout duration is an attribute of the "Password Policy" subentry that is supported by DirX Directory. You also can revise your decision and switch between these choices anytime.
Here is an example of your choices, when the entry is currently locked out indefinitely:
Same situation, but account lockout is not enabled, or it is uncertain, whether account lockout is enabled or not (because e.g. the password policy subentry could not be read):
-
Click Lock account till "lockout duration" expires, if you want to lock out the entry temporarily for the time specified as Lockout duration; Lockout duration is one of the settings the password policy subentry provides (find more about this in the chapter "Password Policy").
-
Click Lock account indefinitely, if you want to lock out the currently selected entry till you possibly decide to re-admit logins by this entry or to lock it till the lockout duration expires.
Notes:
-
The functionality described here presupposes that (as DirX Directory do) the server supports a password policy subentry that provides a number of settings to control how passwords are used and administered, particularly a setting named "Lockout duration" (more exactly: an operational attribute named pwdLockoutDuration). If the DirX Directory Manager plug-in is installed, you are supposed to find more information on the password policy subentry in the according chapter within this help. Moreover, you may also have a look at the server documentation.
-
Since Lock Account… and Unlock Account… only mark the DN to be" locked" or "unlocked", in order to get your setting effective, make sure, that another password policy subentry setting, namely the "Enable account lockout" (pwdLockout) flag is checked off.
-
You are supposed to find the operational attribute pwdAccountLockedTime in the "All attributes" tab of the Properties dialog of the entries of interest. pwdAccountLockedTime being
-
absent means "not locked"
-
set to the 1st of January 1970 00:00:00 means "locked indefinitely"
-
set to any other time/date means "locked, till this time/date + lockout duration has expired". So, changing the lockout duration in the password policy subentry affects all temporarily locked-out entries. A successful login after lockout expiry causes pwdAccountLockedTime to be removed by the server, which means the entry is not affected by modifications of Lockout durations anymore
Reset Password
Allows an administrator to reset a user’s password. Causes a dialog like this one to pop up:
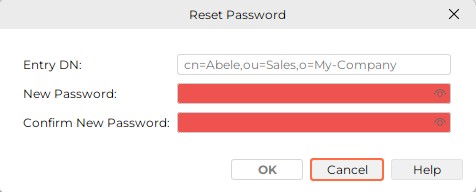
Note that there is a subtle difference between this function and the modify password functionality that is available as an ordinary attribute modification in all properties dialog/pane:
When changing a user’s password with the reset password functionality, the server will be informed of this modification being a "reset". The server will in turn - depending on the password policy currently in place - force the user to update his password before granting him any "productive" operation.
Note that this function is only available if the server indicates its support in the LDAP Root DSE ("Password Policy Control"; Object Identifier, displayed directly or through tooltip: 1.3.6.1.4.1.42.2.27.8.5.1) and if an operational attribute named pwdReset can be set.
Furthermore, if the server keeping the DirX Identity users is set up, the mirrored administrator user must be present in the Connectivity under the RDN dxmC=Users,dxmC=DirXmetahub.
See also: Property Tab "All Attributes", Change Password, Server, User Password
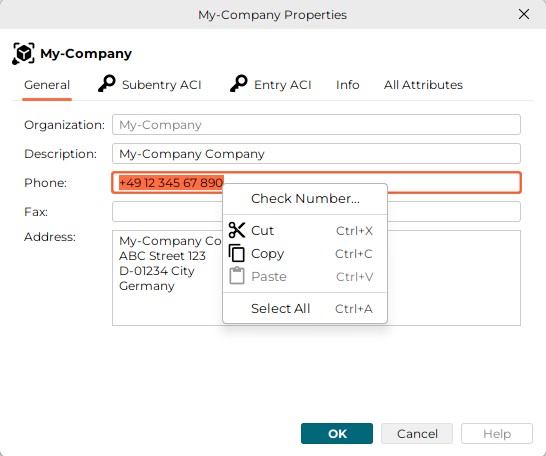
Text Fields
The right mouse button applied to a text field offers:
-
Select all
Selects the entire content of the text field -
Clipboard functions like Cut, Copy, Paste
-
Occasionally, property-specific additional functions like "Check Number" in the example to follow
All Attributes Tab
The all attributes tab that is available at some property panes and property dialogs has a number of functions on the right mouse button:
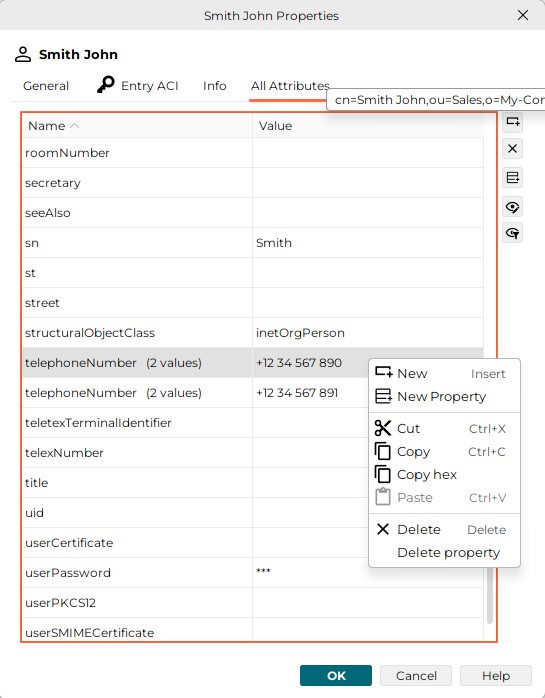
-
Click "New" to insert a new value into a property.
-
Click "New Property" to create a new property.
-
Click "Cut"/"Copy"/"Paste" for clipboard operations that affect the selected property value.
-
Click "Delete" to delete the selected property value.
-
Click "Delete Property" to delete the entire property (same as "Delete", if property is single-valued)
Note the menu changes to the text field menu if you click in the value field of a property that is a text field.
Column Headers of Lists
Applying the right mouse button to a column header in (most) lists allows you to configure the columns that are to be presented. Here is an example:
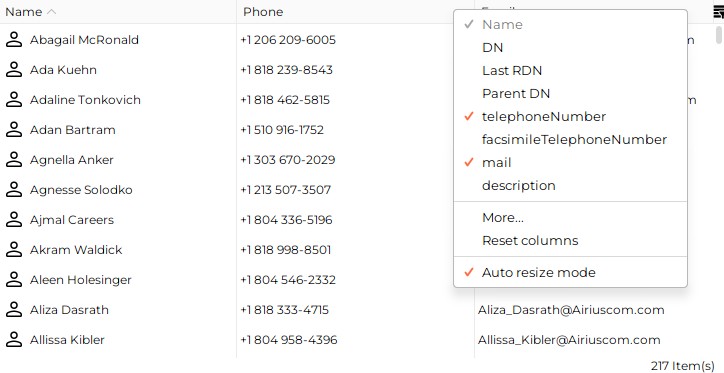
If the number of possible columns exceeds a certain limit, the option "More…" is offered. This option leads to a dialog that offers the complete choice available for the current list.
Recurring (multivalued) attributes display no more than the 10 values.
Note that the attribute value(s) can also be viewed through the related tool tip.
The "Auto resize mode" automatically resizes all other columns, if you resize one column. If switched off, only the column to the left of your mouse cursor resizes.
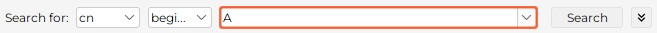
Positioning
A significant number of GUI elements present large enumerations of items, like entries in tree or list panes or elements of combo boxes. The larger the list, the more tedious it can be to scroll down or up to a particular position. In these cases, you can use this application’s positioning abilities to make it easier to handle these enumerations: in tree panes, in list panes and in many non-editable combo boxes, you can position just by typing in one or more characters. A tool tip briefly indicates your typing. When using positioning:
-
Make sure the GUI element in question has the focus.
-
Type, for example, "j" to position to the first item beginning with "j". Repeatedly typing "j" will position to the subsequent items starting with "jjj…" .
-
Type, for example, "joe" to position to the first item beginning with "joe". Don’t pause when typing "joe". Otherwise, you will position to "j" then to "o" and finally to "e".
Abandoning an In-process, yet Uncompleted Operation
Searching
Searching can be abandoned in several ways:
-
By clicking the "Stop" button in Node Toolbar (and Menu)
-
By clicking the "Stop search" button in the search panels. This button usually appears instead of the "Search" button when a search is in process.
Browsing
Browsing can be abandoned by clicking the "Stop" button in Node Toolbar (and Menu).
Properties
Reading the properties of an entry is usually not an operation that lasts for too long. However, there are exceptions:
-
Network problems or server overload may occasionally prevent the server from reacting as usual.
-
Bulky entries (for example, entries having recurring attributes with numerous values) may take a while to get transferred.
For those reasons, you can abandon read property operations by clicking "Cancel" in a dialog-box displayed. Note that this dialog-box is not displayed if the server returns the result rather quickly; and it automatically disappears as soon as the result arrives.
View Panes
View panes are the major building blocks for defining the overall appearance of this application. Their arrangement is defined in a number of configuration files.
Plug-ins may include their own view panes.
This application’s core component provides a number of view panes (note that views normally use only varying subsets of the panes provided), including:
-
Search Pane (closely related to the search dialog)
-
Property Pane (closely related to the property dialog)
There are also container panes, which organize the layout of other panes and do not display any data. The core component provides the following container panes:
Tree Pane
The tree pane allows you to browse hierarchical structures contained in the LDAP directory in a tree-like manner. The tree view is typically accompanied by a list pane or a property pane or a combination of both.
Here is an example of a tree pane:
If the server has implemented operational attributes such as "numSubordinates" and "numAllSubordinates" and if access control grants read access to those attributes, the tree pane may show the number of subordinates and the number of all subordinates for each entry in the tooltip:
-
Entries with no subordinates are considered as "leaves" in the tree, and therefore cannot be expanded further (do a refresh, if you expect that one or more entries have been added below)
-
Tool tips show how many direct subordinates and how many overall subordinates an entry has
-
A sort of pseudo entry may indicate in red that not all entries are available (which typically happens due to a time or size limit or due to access control restrictions)
In combination with searching, you can use the tree for determining a search base - depending on how it is configured - either automatically or by clicking a button located next to the search base field.
To make a multiple selection:
-
To select a range of entries, click the first entry, press the SHIFT key and click the last entry while keeping the SHIFT key pressed.
-
To select a specific entries, hold CTRL key and click the entries you want to select while keeping the CTRL key pressed.
Click a selected entry while keeping the CTRL key pressed to deselect it without affecting the other selected entries.
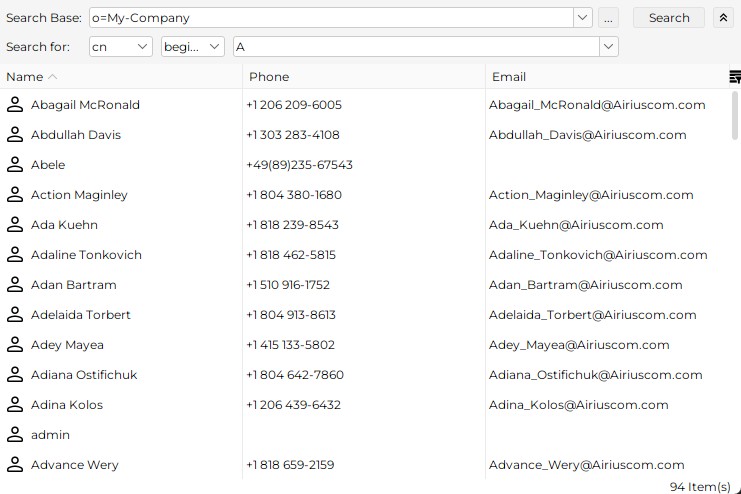
Search Pane
The search pane allows you to specify a search filter and initiate a search causing the server to return all entries (or a subset if there are too many) that match your search filter.
Here is an example of a search pane and a Tree (Browse) pane combined through a tabbed pane:
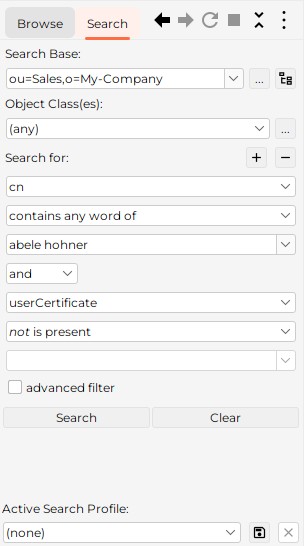
This example shows following components:
-
A tabbed pane, which allows you to switch between browsing and searching
-
Search pane, which allows you to specify a search filter and initiate a search. If the search pane is combined with a tree pane (like in this example), a special feature is available: you can take over the search base from the currently selected entry in the tree pane by clicking the "Get search base form tree" button. Alternatively, the search base may be configured to take the current selection automatically from the related tree pane. You can also use the "…" button to select a value from a tree directly.
The optional server selection field is not configured.
Here is an example of a "slimmed down" search pane:
Read about the other search options in section Standard Dialogs: "Searching".
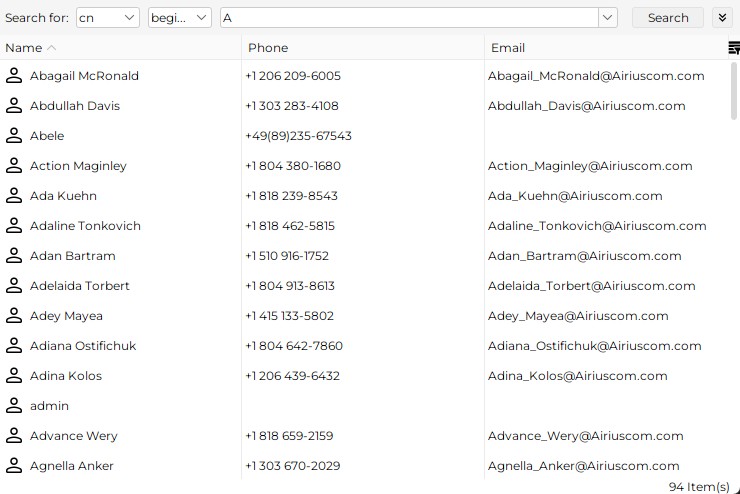
List Pane
The list pane allows having entries (typically search results), more detailed: your choice of their attributes, listed in a table and sorted by the attribute(s) of your choice.
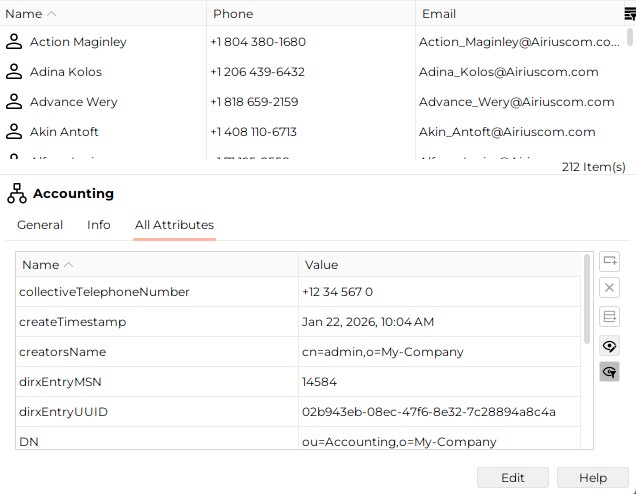
Here is an example of a list pane:

Double-click an entry to display a details dialog for the entry.
To make a multiple selection:
-
To select a range of entries, click the first entry, press the SHIFT key and click the last entry while keeping the SHIFT key pressed. Alternatively, you can click the first entry and hold the left mouse button and draw it downwards or upwards to select a range of entries.
-
To select a specific entries, hold CTRL key and click the entries you want to select while keeping the CTRL key pressed.
Click a selected entry while keeping the CTRL key pressed to deselect it without affecting the other selected entries.
To sort by a column, click the column header. To sort by multiple columns, click the column headers while pressing the SHIFT or CTRL key. The order of sorting is determined by the order in which you click the column headers.
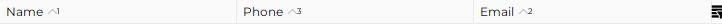
In the example shown here, the list is sorted by three columns in this priority:
-
Priority: Name
-
Priority: Email
-
Priority: Phone
Property Pane
The property pane allows you to read and edit the properties of an entry.
Double-click an entry to display a property dialog (as opposed to a property pane that is embedded into the main window: A property dialog is a separate window that you can resize up to the full screen).
The property pane usually has two modes (read and edit). In read mode, you cannot edit any data.
The clipboard functions cut/copy/paste (cut and paste only in edit mode) are available on a per attribute value basis. These functions also work between different instances of this application. Note that (in tree and list panes) clipboard (and drag and drop) functions are also available for currently selected entries.
Here is an example of a property pane in read mode:
Click Edit to change to edit mode. Note that in edit mode the rest of the GUI is blocked. Plug-ins may add additional buttons here to the bottom of the property pane.
Here is an example of a property pane in edit mode:
Container Panes
Container panes, which organize the layout of other panes and do not display any data. The core component provides the following container panes:
-
Border
-
Split
-
Tabbed
-
Titled
Border Pane
Border panes are used when the size of a pane is to dynamically extend/shorten, as soon as one or more other panes need less/more room due to some action performed on them.
Here is an example of the use of a border pane:
In this example, the border pane (which is invisible) separates a search pane ("Search") from a list pane so that the space that the search pane is to occupy is minimized. The next screenshot shows what happens when you fade-in the search base by clicking the "Show search base" button. A new line appears in the search pane causing it to expand automatically just as much as needed, while the list pane automatically shrinks accordingly.
Clicking the button again makes the search base disappear, the size of the search pane automatically shrinks while the size of the list pane expands; that is, the layout returns to the one previously shown.
Split Pane
A split pane separates two other panes and allows you to increase the size of one pane at the expense of the size of the other one.
Here is an example of a split pane:
This example shows three panes:
-
Above: List Pane
-
In the middle: The split pane (the horizontal bar). The mouse cursor changes to a double-headed arrow when you position it on the split pane. Click and hold the left mouse button and move the mouse up or down to increase the size of one pane at the expense of the size of the other pane. Release the mouse button to fix the new layout.
-
Below: Property Pane
Tabbed Pane
A tabbed pane allows you to switch between two or more other panes through clicking tabs.
Here is an example of a tabbed pane:
This example shows three panes:
-
On top: Two tabs "Browse" and "Search". The "Browse" tab is currently selected showing the tree pane, while the "Search" tab is not selected and therefore the search pane is not on display. Click the "Search" tab to switch to the search pane.
-
Below: Tree Pane
Titled Pane
A titled pane adds a title to another pane, usually on top of the other pane.
Here is an example of a titled pane:
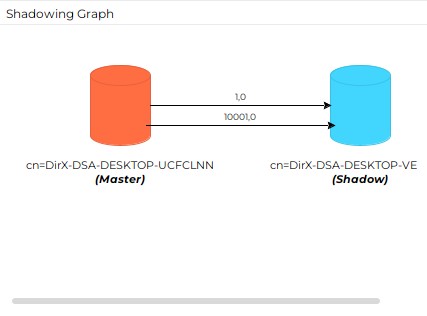
This example shows two panes:
-
On top: Titled pane: "Shadowing Graph"
Titled panes serve just for descriptive purposes. -
Below: the shadowing graph of a shadowing agreement.
Property Editors
When you click a property value in the edit mode of a property dialog or a property pane, this application will show one of the following responses:
-
No response at all, because the property cannot be changed this way.
Here are some examples:-
DN (Distinguished Name)
Use the Rename and/or MoveTo function to change a distinguished name -
cn (Common Name)
Use the Rename function to change a common name -
CreateTimeStamp; CollectiveTelephoneNumber
Changing operational or collective attributes is usually not possible
-
-
The affected property becomes editable. The core component provides property editors for the following attribute types:
-
Attribute with DN Syntax
-
Boolean
-
Country String
-
Directory String (default)
-
Generalized Time
-
Fax Number
-
IA5
-
Integer
-
Jpeg Photo
-
Numeric String
-
Object Class
-
Postal Address
-
Printable String
-
Telephone Number
-
User Certificate
-
User Password
-
There is a number of useful buttons located on the right-hand side of the property dialogs, as shown in the following figure (also indicated are the operations available at the right mouse key):
Use these buttons to:
-
Insert a value. This function may not be present, depending on what type of node is currently selected.
-
Delete the selected property value.
-
Create a new property.
-
Display only editable properties.
-
Exclude empty properties from being displayed
If a property value is too long to be displayed in the visible part of the display field, you can:
-
resize the column or the entire window,
-
position the cursor in the value field and wait for the tool tip to appear.
| The tooltip will be on display only for a while. Alternatively, properties with directory syntax typically offer to view/edit lengthy values in a resizeable dialog. |
Attribute with DN Syntax
The attribute with DN syntax editor allows you to assign a DN to an attribute with DN syntax:
There are additional buttons on the right-hand side of the input field:
-
Properties - opens the properties dialog of the entry whose DN is specified in the value field.
-
Choose a DN - opens a dialog that offers searching and browsing facilities for the DN of interest.
Boolean
The boolean attribute editor allows you to edit boolean attributes. A boolean attribute shows one of the following components:
-
TRUE checkbox
-
FALSE checkbox
Directory String
The directory string property editor is the default editor. It applies to attributes with syntax Directory String and to all attributes with a syntax that does not have a corresponding dedicated property editor.
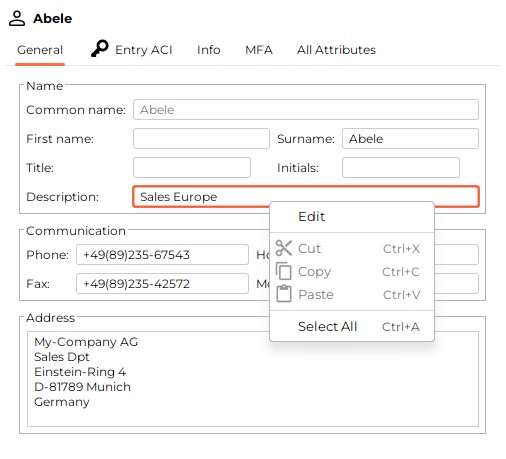
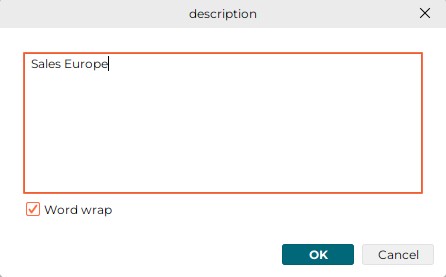
This editor provides a simple editable text field. In order to make reading and editing lengthy directory strings more convenient, the context menu offered through the right mouse button typically includes an "Edit" function that pens a resizeable dialog:
Generalized Time / Generalized Date
The generalized time editor allows you to edit the date and (local) time.

Click the "Calendar" button to open a date picker dialog:
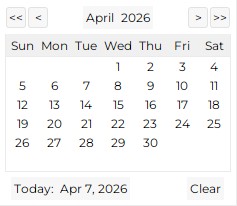
The date picker contains following components:
-
A calendar for selecting the date
-
A "Today" button for selecting the current date
-
A "Clear" button for clearing the date field
-
Button to select current month
-
Button to select current year. To choose a year not in the displayed list, click "(…)". That will allow you to type the year you want to select.
-
Buttons to move to the previous/next month and year
Click the "Clock" button to open a time picker dialog:
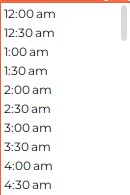
The time picker is a list of time values in 30-minute steps. If you don’t select any time value, the time is set to 00:00.
| The time picker is not displayed for attributes with syntax Generalized Date, since they do not include time information. |
T.50 (IA5)
The T.50 (IA5) editor provides a simple editable text field that is restricted to the character set defined by T.50 (IA5). The allowed characters are Hex 20 to Hex 7E, including “@”.
Integer
The integer editor provides a simple editable text field that does not take any characters other than digits that comply with a number in the range 0 to (232 -1).
JPEG image
Use the Jpeg editor to perform the following actions on JPEG images:
-
View - displays the image in a separate window
-
Import - allows you to select a JPEG image from your file system
-
Export - allows you to save the current JPEG image to your file system
Here is an example of a JPEG editor:
Numeric String
The numeric string editor provides a simple editable text field that does not take any characters other than digits (0 to 9) and space.
Object Class
The object class editor allows you to edit object classes:
| You cannot add, delete or change structural object classes; only auxiliary object classes can be added, deleted or modified. |
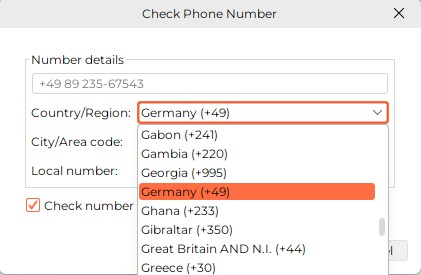
Phone/Fax
The phone/fax editor allows you to edit a phone/fax attribute. Click the value field to change it to inline edit mode. Right-click the value field and select "Check number…" to have an advanced dialog displayed:
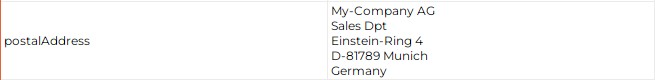
Postal Address
The postal address editor allows you to edit a Postal Address (6 lines of 30 characters):
Printable String (ASN.1)
The printable string editor provides a simple editable text field that is restricted to the character set known as X.208 (ASN.1 Printable String). The allowed characters are A to Z, a to z, 9-0, <space>, ‘)(+,-./:=?
| This editor cannot be applied to email addresses, because the "at" character (@) is not available. |
User Certificate
Use the user certificate editor to perform the following actions on user certificates:
-
View - displays the certificate details in a separate window
-
Import - allows you to select a user certificate from your file system
-
Export - allows you to save the current user certificate to your file system
Here is an example of a user certificate editor:

When clicking the view button, the Certificate Details are displayed:
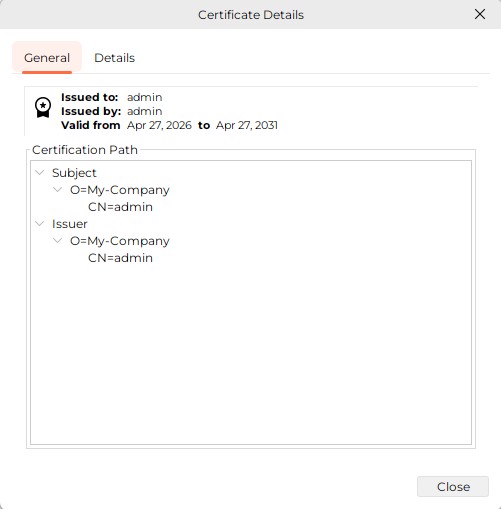
Here the General Tab is selected. At the top of the tab an icon followed by the Issued to, Issued by, and Valid from start date to end date for admin is displayed. Below this information the Certification Path is displayed. Click on the Details Tab to display the certificate details.
User Password
The user password editor allows you to change your own or someone else’s password (depending on the selected entry). Click the value field to display the editor:
Deleting a password works the same way as deleting any other property.
| Multivalued user passwords are not supported by this application. |
Standard Dialogs
The core component provides the following standard dialogs:
-
Binary Attributes
-
Changing Your Own Password
-
Choosing a Distinguished Name
-
Exporting
-
Importing
-
Login
-
Naming
-
Properties
-
Renaming
-
Searching
-
Server
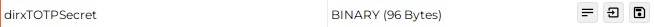
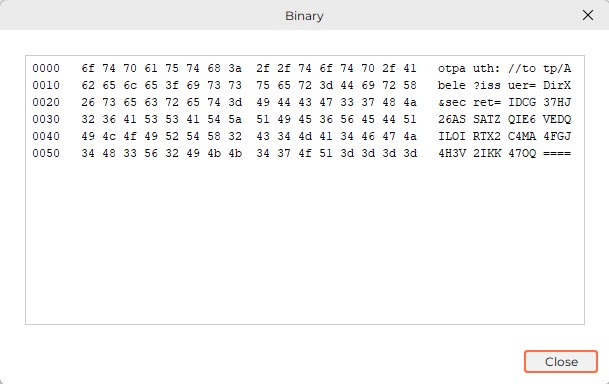
Binary Attributes
Binary attributes other than certificates and jpeg photos are indicated in the all attributes tab like this:
The editor for binary attributes provides the following functions:
-
View - displays the value as hexdump in a separate window
-
Export - allows you to save the value in a file
-
Import - allows you to import a binary value from a file
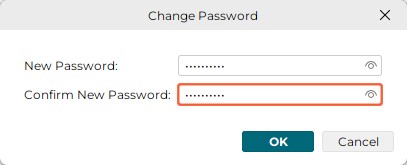
Changing Your Own Password
(To change somebody else’s password, see the topic User Password).
This dialog allows you to change your own password; that is, the password that was used in the previous Login.
Here is an example:
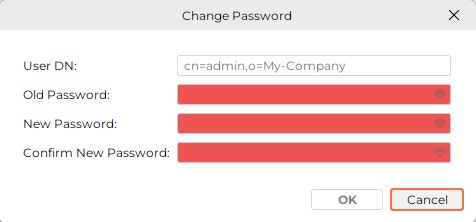
Note that multivalued user passwords are not supported by this application.
Exporting
The Export dialog allows you to specify details regarding the current export, including the file format for the export, the name of the export file, and the entries to be exported. Here is an example of the Export dialog:
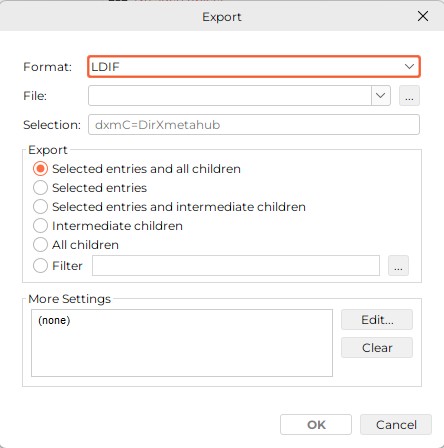
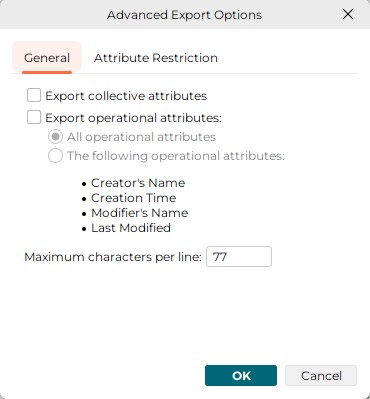
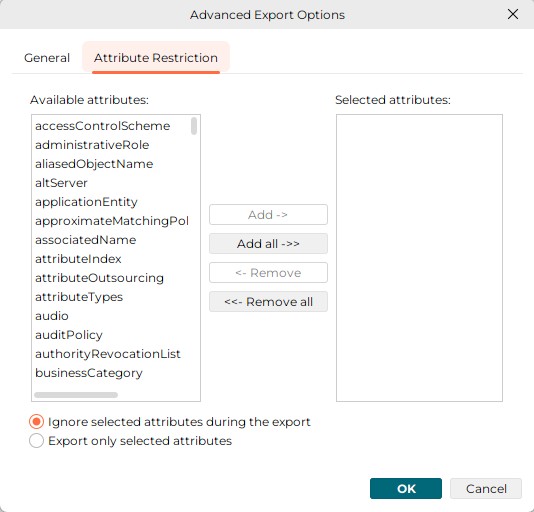
More settings are available through the "Advanced Export Options" dialog open via "Edit…" button in "More Settings" section. This dialog is composed of two tabs: the General tab and the Attribute Restriction tab. Here is an example of the General tab.
The available selections are:
-
Export collective attributes
-
Export all operational attributes
Apart from access control restrictions, the server may decide not to return certain operational attributes, e.g. operational attributes that are expensive to locate. Some servers do not support this option at all. -
Export a named set of operational attributes
-
Limit the number of characters per line (default is 77)
Here is an example of the Attribute Restrictions dialog:
Importing
This dialog allows you to specify details regarding the current import:
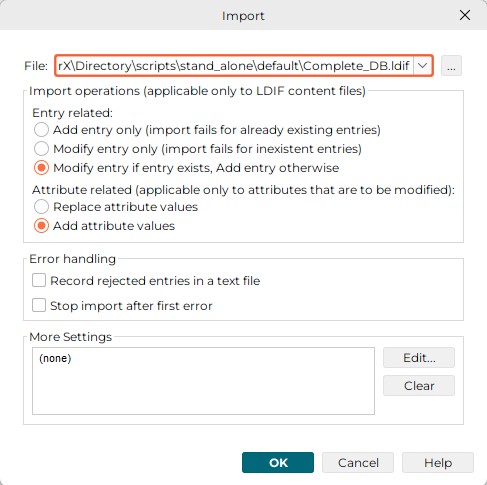
-
The radio buttons "Add entry only", "Modify entry only", "Modify entry if entry exists, Add entry otherwise" apply to LDIF content files only and are ignored otherwise. If the file is recognized as a DMSL v1 file, which is sort of a DMSL content file, only Add entry is possible. In case of modify entry, the affected attribute values, as they exist in the servers' database, will be replaced by the ones found in the file. Attributes that are missing in the import file do not affect the corresponding attributes in the server’s database at all, particularly they do not cause those attributes to be deleted.
-
The radio buttons Replace attribute values and Add attribute values apply only to entries that are to be modified. Add attribute values fails with error
-
For attributes that are single-valued and have already a value in the server’s database
-
For attributes that are multivalued and the set of values possibly stored already in the server’s database and the set of values found in the import file are not disjoint.
-
Check Record rejected entries in a text file if you want to save rejected entries together with the associated error message in an LDIF file. The error messages pre-pend the respective entries in the form of comment lines. Just before it completes, the import function pops up a file selection dialog if there is at least one erroneous entry. If you do not check off this check button, erroneous entries are only displayed in the progress dialog.
-
Check Stop import after first error, if you want to have the import operation discontinue as soon as the first error occurs.
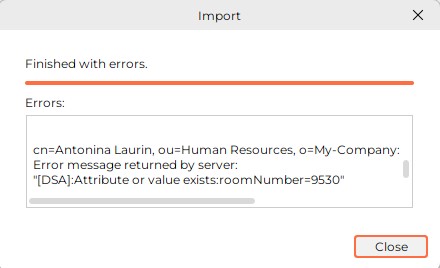
A progress dialog like the one depicted below displays the DNs of the rejected entries and the belonging error messages and allows you to cancel the import any time.
| If the file that is to be imported does not appear to be LDIF or DSML compliant, the import will be refused with an error message. There is one exception: multi-line attributes in LDIF files must be Base64 encoded; however, they are also accepted here, if they appear as text with the individual lines being separated by hex "01". |
More settings are available through the "Advanced Import Options" dialog open via "Edit…" button in "More Settings" section. This dialog is composed of a single tabs: the Attribute Restriction tab. Here is an example:
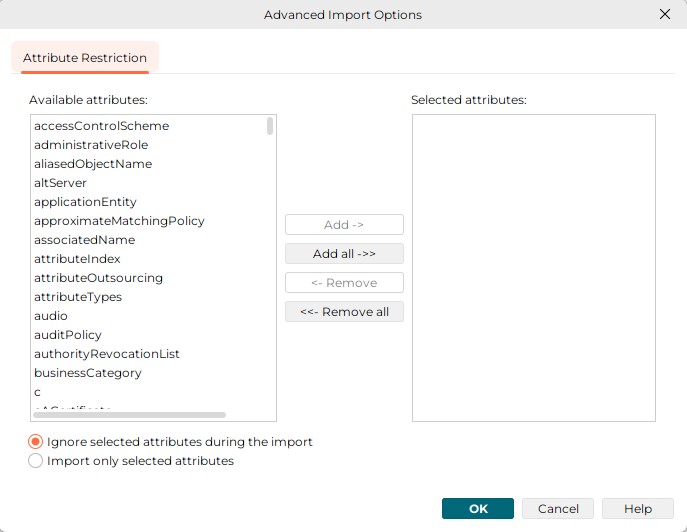
This dialog allows you to restrict the import operation to a specified set of attributes (the ones that appear or - depending on the radio button at the bottom of the dialog - do not appear in the Selected attributes field)
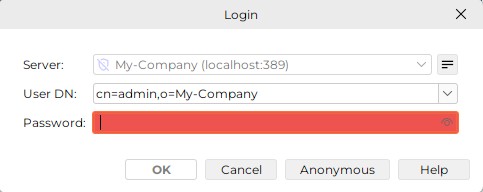
Login
The login dialog allows you to exchange authentication information between you and the LDAP server.
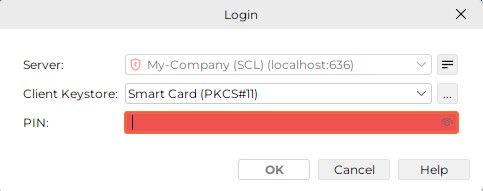
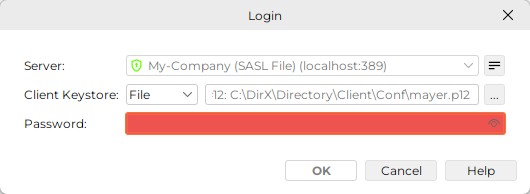
Here are examples for the Login dialog:
-
Performing a simple authenticated or anonymous bind:
-
Performing a simple authenticated bind with Auth code (OTP):
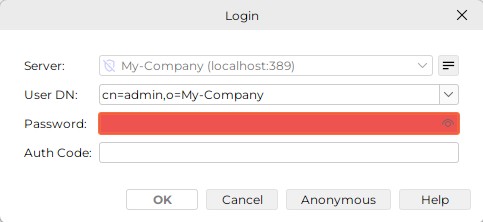
The Auth Code is still only necessary for users that have MFA (Multi-Factor Authentication) enabled (have object classdirxTOTPUserset anddirxTOTPSecretattribute set). -
Performing a smart card login:
-
Performing a file based SASL EXTERNAL bind:
In order for this application to be able to connect to a server, you must:
-
Specify a server
Click the "New…" button in the Manage Server Profiles dialog to create a server profile, if no suitable profile is available, or click the "Properties" button to edit the currently selected profile. -
Specify login information
-
Specify a DN (Distinguished Name) and a password for a simple authenticated bind or alternatively log in "anonymously". If "anonymous" is checked in the selected server profile, the DN and password fields should be grayed out and are not editable.
-
For smart card logins, insert the smart card into the reader and specify the PIN.
-
For file based SASL EXTERNAL binds, press the "…" button and browse to the file location of the JavaKeyStore (.jks) or PKCS#12 formatted container (.p12) with your private key and public key certificate(s) and specify the local passphrase (the password) that protects the .jks or .p12 file.
| You may be offered read access only, or read and write access - depending on the access policy settings in the server dialog. |
Naming
Use the naming dialog to assign a name to an object that you are creating.
Here is an example:
Properties
Summary Properties
Properties are typically displayed and edited in
-
A property pane (embedded into this applications main window)
and/or -
A properties dialog (popping up in an own window you can resize up to the full screen, when right-clicking an entry and selecting "Properties" or when double-clicking an entry).
For the functionality provided for properties, it does not really matter, if you work with property panes or prefer property dialogs. The use, however, may be different in details: while the property pane typically distinguishes between a read mode and an edit mode, the property dialog usually knows only one mode.
By default, a generic property dialog/pane has these tabs:
-
An Info tab
-
An "All Attributes" tab
The properties dialog/pane may be "generic" (i.e. it has the default tabs mentioned above) or customized. It displays details of the currently selected entry and may allow you to edit some of them (editable fields are ones that are not grayed out). A Close button in place of the OK and Cancel buttons indicates that the entry itself is not editable. Alternatively, the property dialog may make a distinction between view mode and edit mode. In this case you are to face buttons like the ones described in property pane.
The clipboard functions cut/copy/paste (cut and paste only in edit mode) are available on a per attribute value basis. Note that (in tree and list panes) clipboard (and drag and drop) functionality is also available for currently selected entries.
The properties dialog is usually available by:
-
Right-clicking the entry of interest
-
Double-clicking the entry of interest
-
Using the menu
See the topic Property Editors:Summary to learn about the buttons shown in the right-hand side of the properties dialog, as shown in the figure here.
Also see the topic Property Editors:Summary to learn how to view property values that do not fit into the value field.
Customized tabs
This application provides a customized tab for some types of objects (Group, Internet Organizational Person, Organizational Person, Organizational Unit) that adds to the Info and all attributes tab. Plug-ins may provide property panes/dialogs that are even more customized.
See also: Property editors.
Property Tab "General"
For a number of common object classes, additionally a "General" tab is shown accommodating the attributes considered most interesting. If more than one object class applies, the most specific one wins.
Examples:
-
Person
-
organizationalPerson
-
inetOrgPerson
-
organization
-
organizationalUnit
-
groupOfNames
-
groupOfUniqueNames
Person
The pre-configured "General" tab for entries whose object class is "Person" looks like this (unless the entry has additional object classes like organizationalPerson):
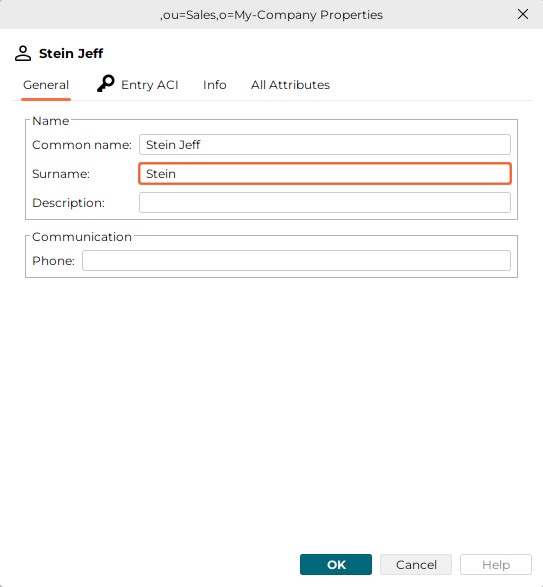
organizationalPerson
The pre-configured "General" tab for entries whose object class is "organizationalPerson" looks like this:
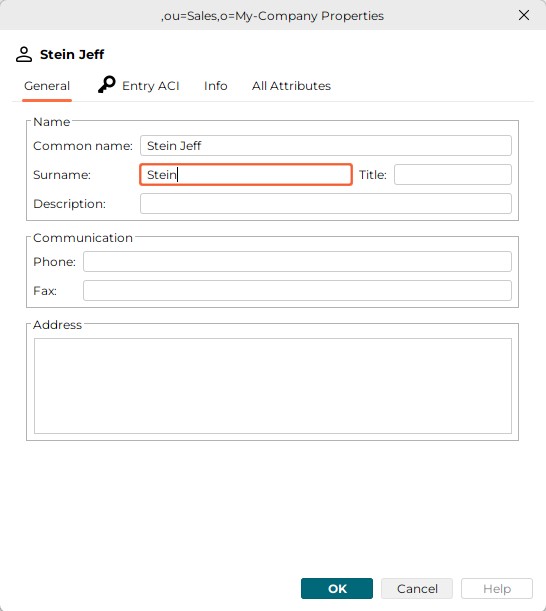
inetOrgPerson
The pre-configured "General" tab for entries whose object class is "inetOrgPerson" looks like this:
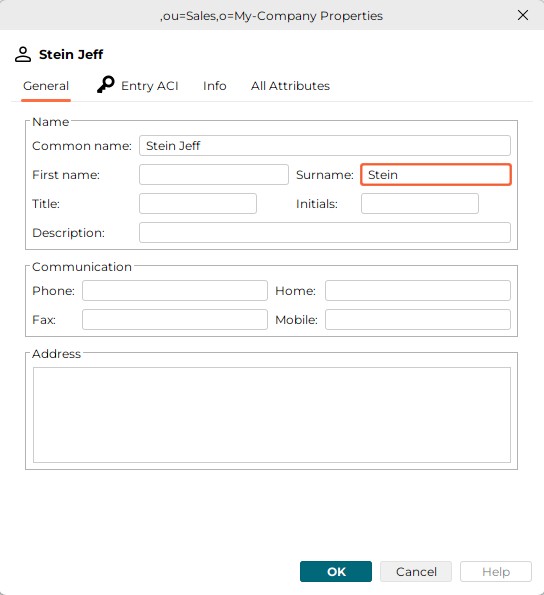
organization
The pre-configured "General" tab for entries whose object class is "organization" looks like this:
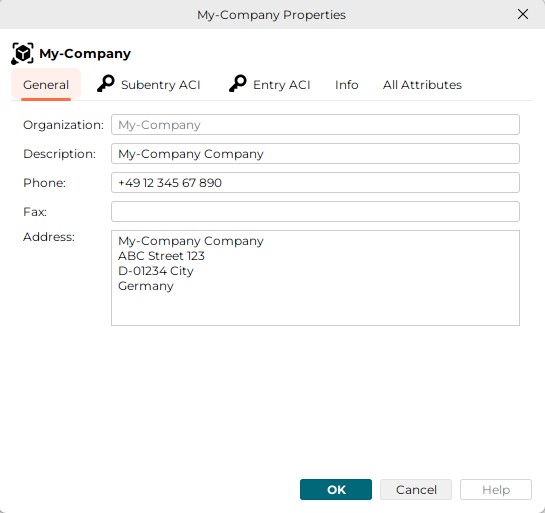
organizationalUnit
The pre-configured "General" tab for entries whose object class is "organizationalUnit" looks like this:
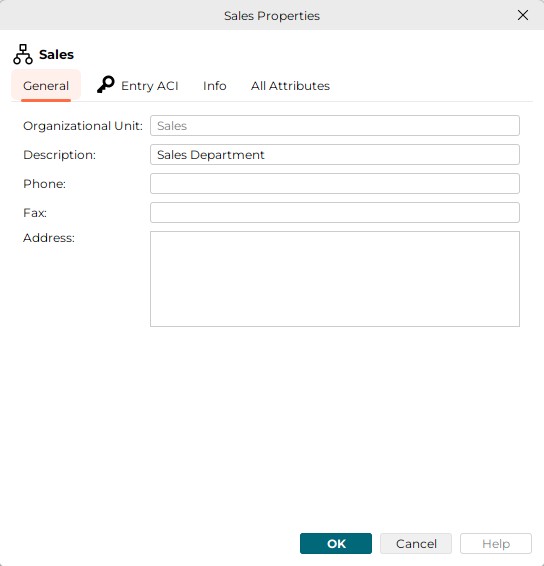
Property Tab "All Attributes"
The "all attributes" tab displays all attributes including the ones that are shown on the other tab(s).
Example:
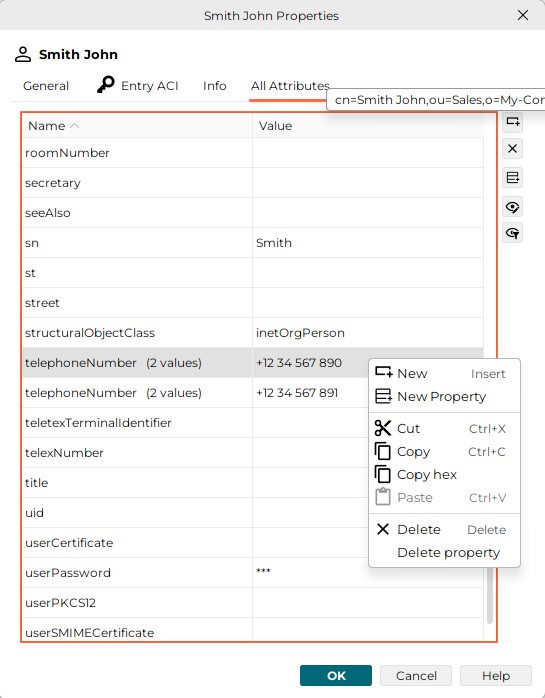
See also Property Editors (for a description of the right-hand convenience buttons), Property Pane, Property Dialog and All Attributes/Right Mouse Button.
For Password modifications, see also: Change Password, Reset Password, User Password, Server.
If the name column is selected, it is possible to position to a particular attribute by typing the initial letter(s).
For attributes with more than one value, the number is displayed in the name column - usually the first column - to the right of the attribute name (administrativeRole (4 values)):
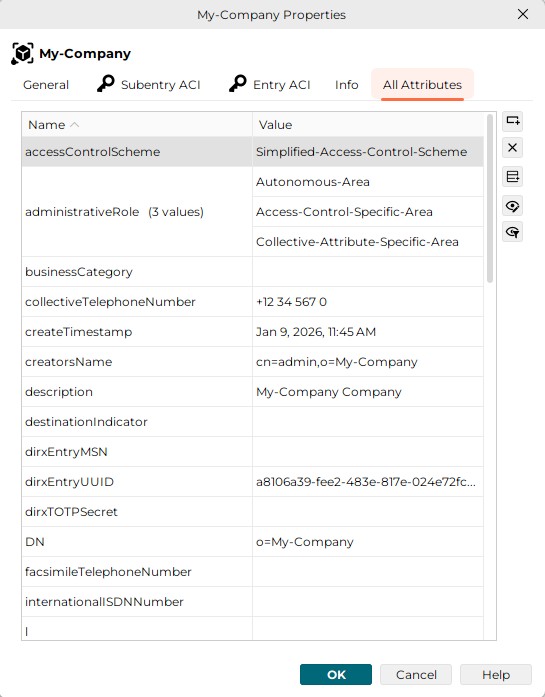
If the attribute name is outside the currently visible part of the pane/dialog the number of values is displayed as tool tip:
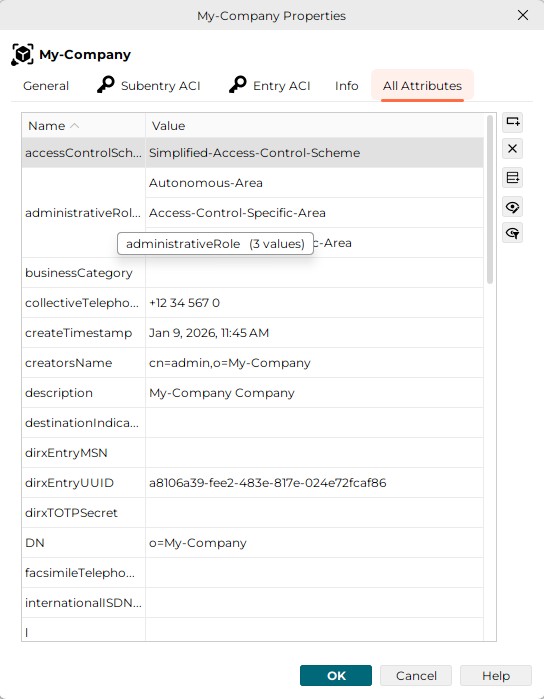
Property Tab "Info"
In the following example the "Info" tab of a new entry with object class person is displayed:
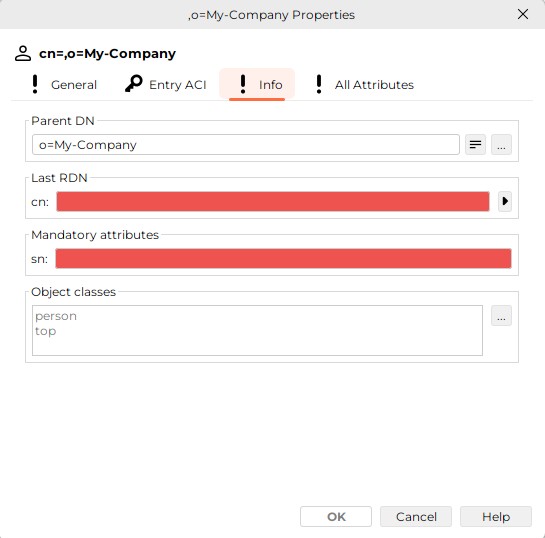
This tab displays
-
The Parent DN
-
The last RDN (pink, if missing because this is a mandatory field)
-
All additional mandatory attributes (pink, if missing; there is just the mandatory attribute surname (sn) in the screenshot above). Mandatory attributes get additionally inserted automatically, as soon as another auxiliary object class with mandatory attributes is added.
-
All Object Classes
See also Property Dialog, Property Editors and Property Pane.
Property Tab "MFA"
The "MFA" tab is shown when the entry has the object class dirxTOTPUser. It contains the dirxTOTPSecret attribute shown as a QR code and as binary text in a text field, from which it can be copied to the clipboard. The QR code can be scanned by an MFA app on a smartphone, which then can be used for 2FA.
The dirxTOTPSecret is not generated immediately after adding the dirxTOTPUser object class, but only after saving the entry. So if you add the dirxTOTPUser object class to an existing entry, you need to save the entry first and refresh. When removing the dirxTOTPUser object class, the dirxTOTPSecret is not deleted immediately, but only after refreshing the entry.
|
You may see this warning in the UI until the dirxTOTPSecret is generated and displayed:
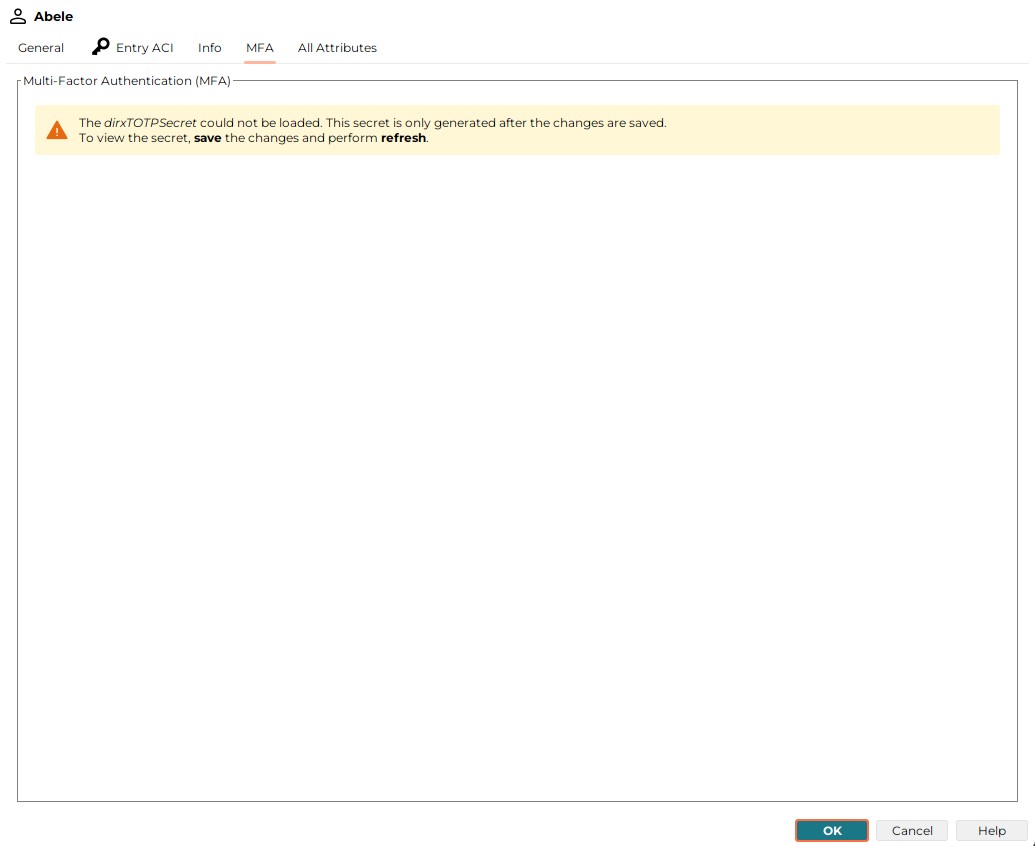
After the dirxTOTPSecret is generated, the MFA tab looks like this:
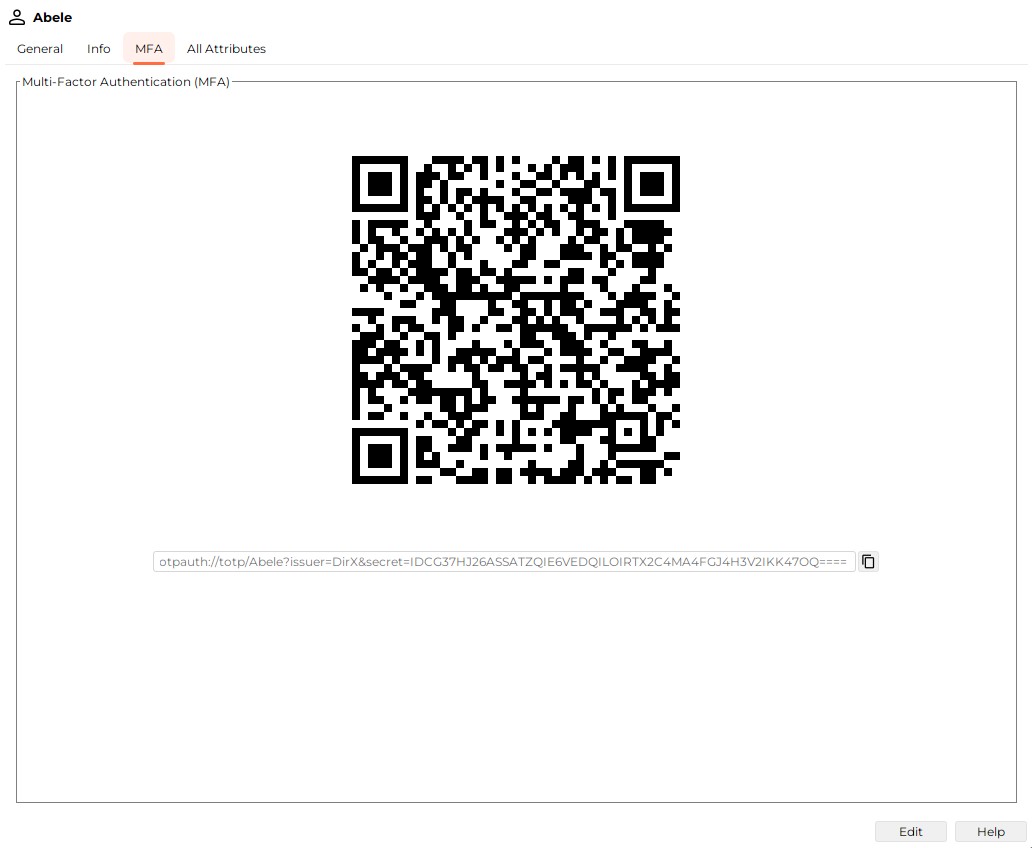
Renaming
The renaming dialog allows you to rename the currently selected object. Note that the checkbox "Retain old name" and the button do not appear unless you are renaming an LDAP entry.
Here is an example (which illustrates renaming an LDAP entry):
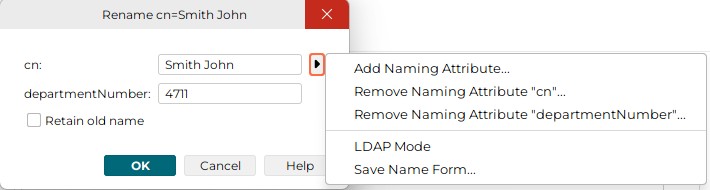
The menu item contains the following selections (the menu appears when you click the "Right Arrow" button):
-
Add Naming Attribute
Adds a line that is to pick up an additional naming attribute (in the example dialog, the line "l: Atlantis" resulted from a previous use of this function) -
Remove Naming Attribute "…"
Only present if there is more than one naming attribute on display -
LDAP Mode
Changes the appearance of this dialog according to the screenshot shown next. -
Save Name Form…
Stores the current name form locally for reuse when another object of the same type is to be created.
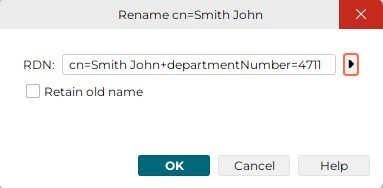
This is the same menu item as the previous example, but in LDAP notation. In this mode, there is only one function available through the right mouse button. This function changes the appearance of the dialog back to the look shown in the previous example.
Searching
There are two sorts of search dialogs available (may occur combined, too):
-
The rather simple search that is supposed to be sufficient for most cases
This dialog has a sub dialog that allows you to specify "compound object classes" -
The full-featured advanced search that allows you to express quite complex searches
Simple Search
This dialog is displayed for example by the search function that is usually available on the right mouse button. The elements used in this dialog may likewise show up in a search pane (except for the search result, which is shown separately in an associated list pane).
Here is an example:
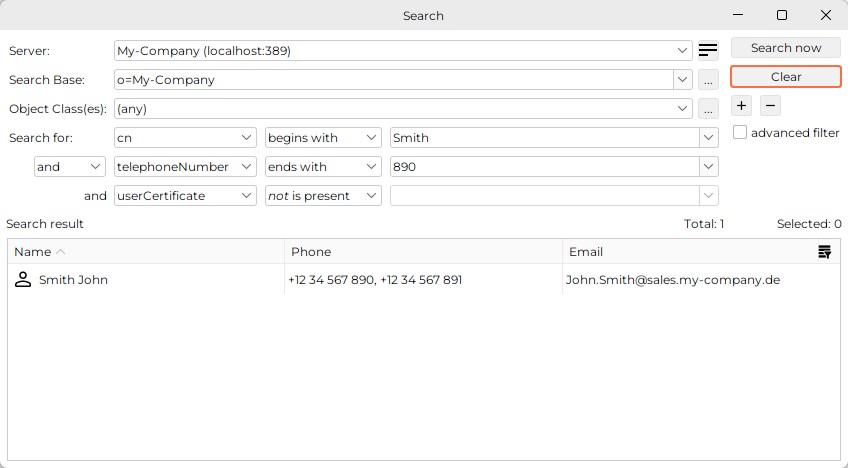
This dialog contains all or a subset of the following elements:
-
A field to select the server to be addressed (suggested: the current server)
-
A field to define the search base (suggested: the current entry)
Click "…" (the one located to the right of the search base field) to display a dialog that allows you to choose a value from a tree. -
A field to choose the object class(es) the returned entries must have
The choice of filter attributes offered in the "Search for" combo boxes that follow beneath depend on the object class(es) chosen here. If only one object class is selected, all filter attributes are offered that are (directly or indirectly) assigned to this object class (disregarding that attributes may generally be disabled). If more than one object class is selected (like in the example above), all filter attributes are offered that are (directly or indirectly) assigned to at least one of those object classes. Regarding the sample, all filter attributes are offered that are assigned to object class "InetOrgPeron" or to object class "pkiUser" (or both).
If the object classes are associated with "AND", a corresponding search result contains only entries having each of those object classes. If they are associated with "OR", a corresponding search result contains only entries having at least one of those object classes.
Not really an object class is "(any)": Choosing "(any)" causes all available filter attributes to be offered. The object class used behind (any) is "*" (LDAP jargon). Note that this means that only entries having an object class can be found. LDAP entries must have at least one object class anyway, violations of this rule are rather uncommon.
By default, the object class(es) combo box allows you to choose one single object class (or the pseudo object class "(any)"). However, you can define kind of "compound object classes" after pressing the "…" button that is located to the right of the object class field. The object class compositions you define this way are sorted ahead of the ordinary object classes in the object class combo box. You can assign a name to your definition. In this case, you can check how you have defined the current compound object class by looking at the tooltip of the object class(es) combo box. Regarding the sample above, the name is "People", the tooltip shows "inetOrgPerson OR pkiUser"
Auxiliary object classes are identified by a suffix such as "(aux)", whereas structural object classes lack any characteristic suffix. -
Fields to specify a filter attribute, filter type and filter value, e.g. Common name begins with Smith
This element may appear several times (controlled by two buttons that enable you to expand or collapse the number of these elements: "+" and "-". You can associate these elements by either logical "and" or logical "or". Mixing "and" with "or" is not possible. Filter types usually also offer negations (indicated by a prefixed "not") as shown in the picture below:
-
Buttons to initiate a search or to cancel a search that has not yet completed
-
A "Clear" button that causes the attribute filter elements to collapse to one element and delete its filter
The dialog depicted above is technically a "frame", not a "dialog" (for example, it has no OK, Cancel or Close button), a differentiation that is generally ignored in this help. Alternatively, it can also occur as a real dialog; in that case, the search result field would be missing.
Compound Object Classes
A dialog like the one depicted below is popping up after pressing the "…" button that is located to the right of the object class(es) field in the simple search dialog or in the search pane. It allows you to define a logical association (AND/OR) of several object classes to be used as a filter element in a search.
The main idea is that you compose one structural object class with one or more related auxiliary object classes. For example, you could specify "inetOrgPerson AND pkiUser". In this case, you would search for entries having both object classes, and you would only be offered the filter attributes that are (directly or indirectly) assigned to inetOrgPerson or to pkiUser, e.g. you would be offered "telephoneNumber" (which is commonly assigned directly to organizationalPerson and - by way of inheritance - indirectly to inetOrgPerson) as well as "userCertificate" (which is commonly assigned to pkiUser). This would otherwise only be possible with object class "(any)".
You can also compose two or more auxiliary object classes or two or more structural object classes, respectively. The latter makes sense at most if you associate them with "OR" (otherwise all object classes but one would be superfluous (if they are all in one inheritance line,) or you would never get a search result (if not)).
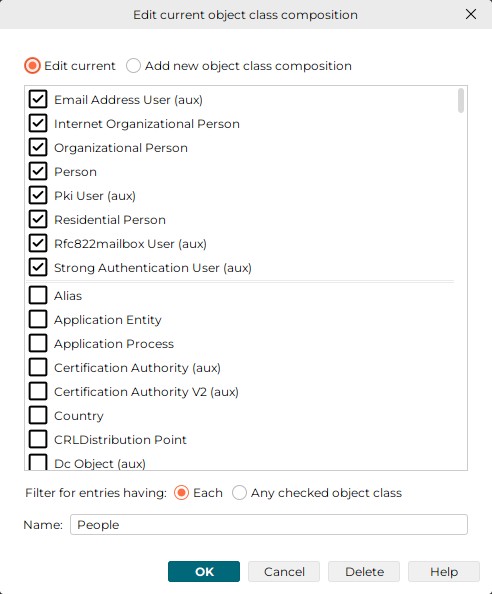
Auxiliary object classes are identified by a suffix such as "(aux)", whereas structural object classes lack any characteristic suffix.
Check the Edit current check box if you want to edit a previously defined compound object class. Check the Add new object class composition check box if you want to create a new one.
Check the Each check box if you want to associate the checked object classes with "AND". Check the Any checked object class if you want to associate them with "OR"
Click the Delete-button if you want to delete the currently selected object class definition (note that you cannot delete an "ordinary" object class that was not defined by yourself but was obtained from the schema).
You may or may not assign a name to your object class definition that is to be shown in the object class(es) combo box of the search dialog or the search pane instead of a list of the checked object classes. The tool tip will still provide you with information concerning the involved object classes and their logical association.
Advanced Search
At appropriate places, a search dialog like the one depicted below may be present; it is intended to allow for both, composing filters complex enough to meet even the most sophisticated needs and for comfortably composing rather ordinary filters. Unlike this filter type, the simple filter is somewhat restricted in order to be able to satisfy the majority of use cases particularly conveniently.
Example of an advanced search (without supplementary simple search tab):
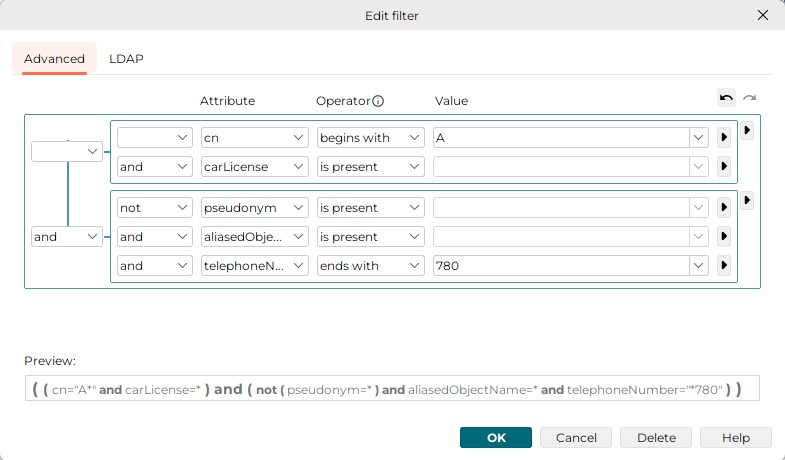
The advanced search allows to:
-
Associate attributes with values through operators like "begins with", "ends with", "equals", "contains", "is present"
-
Combine such associations with "not", "and", "or", "and not", "or not" (use the "inner" "Right Arrow" buttons)
-
Group such associations and combine those groups analogously (use the "outer" "Right Arrow" buttons)
-
Recursively nest groups (use the "outer" "Right Arrow" buttons)
-
Delete the current row or group row (use the "Right Arrow" buttons)
You can find the "Undo"/"Redo" buttons in the top-right.
The tab completes with a preview field that shows the resulting logical expression is intended to help you keep track.
The text entered in the Value field is treated as the search value itself. If the value contains the special characters backslash "\", left parenthesis "(" or right parenthesis ")" they are internally changed to the corresponding escape sequences "\5c", "\28" or "\29". However, if a backslash is followed by two hexadecimal digits, it is treated as a valid escape sequence and the backslash is kept as it is.
For example:
-
"\abc" will be kept as "\abc" because "\ab" is a valid escape sequence. The filter will then search for a two-character text beginning with a character with hexadecimal code AB followed by the character "c".
-
"\a\b\c" will be replaced with "\5ca\5cb\5cc" since none of "\a\", "\b\" or "\c" is a valid escape sequence. The "\" character will then be replaced with "\5c".
The Attribute field can also contain virtual attributes; for example, “dxrOptions(location)”. When converting these attributes to the LDAP search expression, the name part in the parenthesis is converted to the attribute value.
When parsing the virtual attributes from the LDAP search expression to the Attribute combo, it is first verified whether the search expression matches some of the virtual attributes in the Attribute combo list. If the LDAP search expression matches a virtual attribute, it is treated as a virtual attribute. If the LDAP search expression doesn’t match any virtual attribute, it is treated as standard attribute.
For example:
-
If the search expression is "dxrOptions(location) equals Munich", the resulting LDAP search expression is "(dxrOptions=location Munich)".
-
Parsing the LDAP search expression "(dxrOptions=location Munich)" results in "dxrOptions(location) equals Munich" since the "dxrOptions(location)" is present in the combo box selection list and thus recognized as a virtual attribute.
-
Parsing the LDAP search expression "(dxrOptions=locate Munich)" results in "dxrOptions equals locate Munich" since the "dxrOptions(locate)" is not present in the combo box selection list. Thus, the attribute is recognized as pure "dxrOptions" without any further specification.
The dialog also offers a tab addressing those who are accustomed to genuine LDAP syntax. This tab allows you to enter the filter in the LDAP filter expression format. The search expression is taken "as is," and you are fully responsible for its correctness.
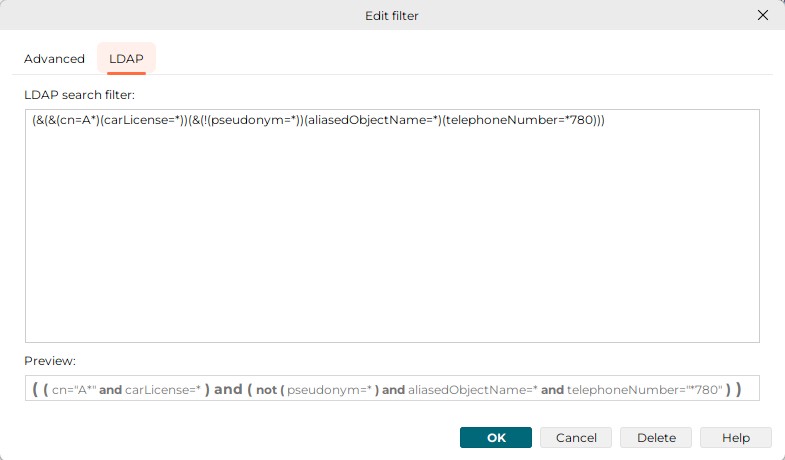
When switching from the LDAP tab to the Advanced tab, the search structure in the Advanced tab is reconstructed from the LDAP filter expression in the LDAP tab.
When switching from the Advanced tab to the LDAP tab, the LDAP search expression is created from the search structure only if some modifications were made - the "undo" button in the Advanced tab is enabled. If the "undo" button is disabled, no changes were made and the LDAP search expression in the LDAP tab remains unchanged. This feature allows you to enter any search expression without overwriting from the Advanced tab.
Server
The server dialog allows you to specify server-specific information in a "Server Profile", particularly information needed to connect to an LDAP server. Server profiles often correspond to view groups or views. However, it is also possible to address different servers (or the same server with different server profiles settings) within a single tree pane.
Plug-ins may categorize server profiles; that is, they can ensure that you can only see server profiles of a certain category within the view groups, views, nodes in tree panes under control of a plug-in. Category names are not displayed. New server profiles you create in a context where a category is in effect already, implicitly inheriting that category.
The settings you can make here are organized into these tabs:
-
General - Deals with LDAP connection related settings
-
Options - Primarily deals with controls that are to be passed to the LDAP server along with respective LDAP operations
-
Visibility - Deals with the visibility of attributes and object classes in search panes and search dialogs
-
Password - Allows you to specify, if
-
the additional password of DirX Identity users should be managed
-
affected users should be notified by mail on password reset
-
-
LDAP Root - Displays what the server returns if asked for "LDAP Root".
General
Here is an example of the dialog’s "General" tab:
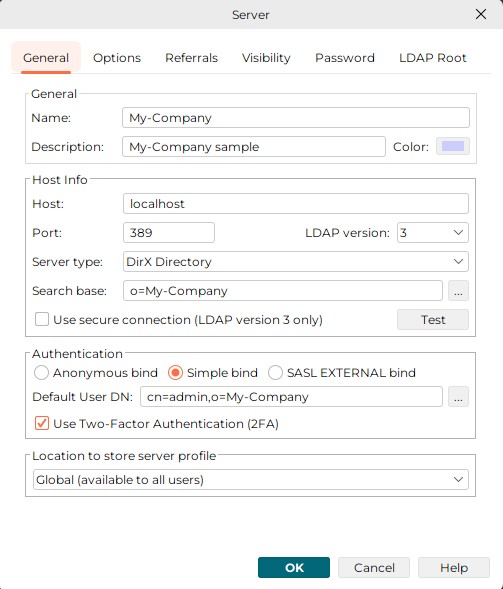
This tab deals with LDAP connection related settings and contains the following fields:
Name: name of this server profile
Description: any additional information you might consider helpful
Color: the color for this server profile
Host: host name or IP address
Also possible: a blank-separated list of hosts with or without complement port number, e.g. "localhost:389 111.222.333.444 666.777.888.999:636"
In this case, this application will connect to the first address it can successfully connect to, starting with the first one. If the port number is missing, the value specified in the following field (Port) will be used.
| When changing Host or Port here, the settings related settings in the password tab may need to be changed as well. |
Port: port number
By default, the server listens to port 389 or - if SSL is enabled - to port 636.
|
The designated port may be occupied by a different program. In this case, the LDAP server cannot start up with that port and must be assigned a different one. The server side configuration may have been changed to correct a conflicting port problem or for another reason. In this case, the LDAP server should be able to start up, but you need to specify the corresponding port number here. |
LDAP version: LDAP protocol version (normally: 3)
Server Type
This field is only present, if the "DirX Manager" plug-in is in place. There are two possible values: "DirX Directory" and "Other". The functionality DirX Directory Manager offers depends on this selection:
-
The subsequent field is called "Base DN", if server type is "Other" and "Search Base" otherwise.
-
Several functional areas work only with suitable versions of DirX Directory. These functional areas include:
-
Database (found in the DirX Directory Manager "Schema" view)
-
LDAP cache configuration (found in the Dirx Directory Manager "Configuration" view)
-
Password Policy (found in the DirX Directory Manager "Configuration" view)
-
Replication (DirX Directory Manager "Replication" view)
-
Schema is editable (DirX Directory Manager "Schema" view)
What functional areas ("features") are mapped to what vendor versions is specified in the file config\DirX.policy. Note that this release of DirX Directory Manager is not necessarily able to interwork with future releases of DirX Directory particularly regarding the functional areas mentioned above.
-
Also affected by the server type is the following field (Search Base/Base DN).
Search Base (displayed if server type is "DirX Directory") resp. Base DN (displayed, if server type is "Other" or if the DirX Directory Manager plug-in is absent)
-
Browsing
Ineffective, if Server type is "DirX Directory": Regardless of what is specified here, the tree panes always display the context prefixes as top nodes.
Server type is "other": The DN specified here is used as (only) top node in tree panes. -
Searching
The DN specified here is used as the default search base.
Use secure connection
In order for a secure connection to work, you must ensure that a suitable certificate is available in a local key store. By default, a test certificate is used that matches the default the DirX Directory LDAP server uses. Note that this certificate is only meant for demonstration. Read more about this in the chapter SSL/TLS.
Anonymous bind: to have this application try to connect without credentials (anonymously)
Simple bind: to have this application try to connect over a simple authenticated bind with credentials
SASL_EXTERNAL bind: to have this application try to connect over a SASL-authenticated external bind. If you select this option you must specify the client keystore. The client keystore is either stored in a File or on a Smart Card (PKCS#11). Using a file is intended for demonstration or testing purposes. For details on how to perform a smart card login with DirX Directory Manager, see "Smart Card Login" above.
Default User DN: The DN you typically use to log in
Use Two-Factor Authentication (2FA): to have this application try to connect over a simple authenticated bind with credentials and an auth code (OTP). If you want to bind with a user which has 2FA set up (has object class dirxTOTPUser and attribute dirxTOTPSecret), you need to check this option.
Location to store server profile: the choice of locations may vary depending on the plug-in that is behind this dialog. Generally, the available choices should be all or a subset of:
-
User Home: This profile is to be used only by you
(the profile will be stored in your home directory) -
Global: This profile is to be offered all users using the same machine
Options
Here is an example of the dialog’s "Options" tab:
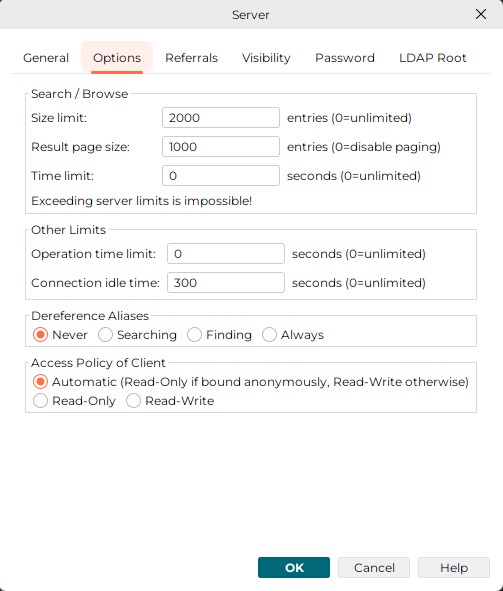
This tab primarily deals with controls that are to be passed to the LDAP server along with respective LDAP operations:
Limits
-
Size limit: the maximum number of entries the LDAP server is to return as the result of a search or browse operation. The value 0 is unlimited number of entries. Note that the server may return fewer entries, since it may have a more restricted server-side size limit. As for DirX Directory, specify a size limit for the LDAP server in the LDAP configuration subentry, for the X.500 server in the user policy attribute(s).
-
Result page size: the maximum number of entries of one page of the search result. The value 0 disables paging.
-
Time limit: the maximum period of time granted to the LDAP server to complete a search or browse operation. The value 0 is unlimited number of seconds. Note that the LDAP server may have a more restricted server-side time limit. Also, the server may not observe this limit strictly.
-
Note that if a size or time limit takes effect, the remaining (unread) entries can come from anywhere within the range of entries on display; that is, in the result that the server returns, some existing entries may be omitted, while others that are alphabetically behind may be present.
-
Operation time limit: under rare conditions, a server may fail to return any result within a reasonable amount of time, even if other limits have been set. The operation time limit limits this application’s "patience" with the duration of an LDAP operation. If the patience is exhausted, this application, in order to avoid getting blocked, displays a message and discards the result. Once the operation time limit has been reached, a corresponding result that arrives late will be disregarded. The value 0 is unlimited number of seconds.
-
Connection idle time limit: Limits the amount of time this application is to maintain a connection with the server when there is no traffic on the connection. The value 0 is unlimited number of seconds. Note that the server may have a more restrictive connection idle time limit and cancel the connection on its own.
Note that if a connection has been canceled and the user initiates another operation, this application will normally try to implicitly re-establish that connection.
De-referencing aliases. Possible values are:
-
Never: specifies that aliases are never de-referenced
-
Searching: specifies that possible aliases are de-referenced in the search result
Note that when intending to manage (particularly delete) alias entries, you should not have checked Searching or Always, since then the server does not return any alias entries. Otherwise, you run the risk of mistakenly deleting the original entry rather than the alias with the alias pointing to an entry that no longer exists. -
Finding: specifies that the search base is to be de-referenced if it happens to be an alias
-
Always: specifies that aliases are always de-referenced
Note that when intending to manage (particularly delete) alias entries, you should not have checked Searching or Always, since then the server does not return any alias entries. Otherwise, you run the risk of mistakenly deleting the original entry rather than the alias with the alias pointing to an entry that no longer exists.
Access Policy
An LDAP server primarily grants and denies access rights based on access control information stored at the server side. This application normally cannot determine a particular user’s access rights. By default, the GUI does not offer any add/modify operations to users logging in anonymously and does offer those operations to users logging in with credentials. This behavior is not always appropriate and can therefore be changed. Possible values are:
-
Automatic: Apply the default policy.
-
Read-only: Do not offer add/modify operations no matter how the user has been logging himself in.
-
Read-Write: Offer add/modify operations even if the user has been logging himself in anonymously.
Referrals
Here is an example of the dialog’s "Referrals" tab:
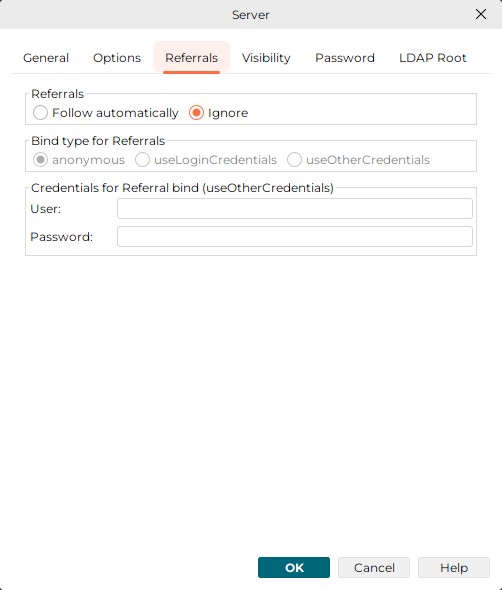
This tab deals with the handling of referrals.
Referrals
A server may return referrals pointing to other servers as part of a search result, thus indicating that one or more other servers should be consulted in order to complete a search operation.
-
Follow automatically: the application automatically follows any referrals returned by the server that points to a different server until the "referral hop" limit is exceeded. The referral hop limit defaults to 10. This application does not support modifying the referral hop. Note that following referrals automatically does not work unless the server to which the request is referred accepts anonymous binds.
-
Ignore: Referrals returned by the server are discarded.
Bind type for Referrals
Here you specify which bind you want to use for following the referrals.
-
anonymous: an anonymous bind is used for following referrals. This is the default.
-
useLoginCredentials: The same credentials you used for login to DirX Directory Manager are used.
-
useOtherCredentials: the credentials defined in “Credentials for Referral bind” are used.
Visibility
Here is an example of the dialog’s "Visibility" tab:
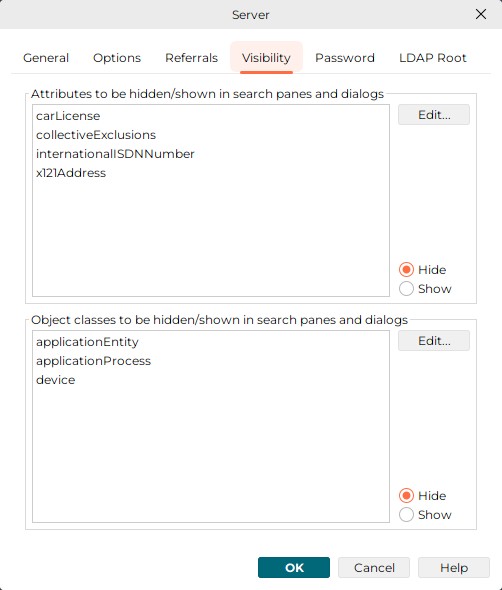
This tab deals with the visibility of attributes and object classes in search panes and search dialogs.
The schema usually provides quite a number of object classes and attributes you never intend to use in searches - and whose appearance in the respective combo boxes of search panes and search dialogs you may find bothersome. This dialog along with the subdialogs that pop up when you click one of the "Edit…" buttons allows you to hide unwanted object classes and attributes in those combo boxes. You can either select all elements you want to have hidden (which means that all remaining ones are shown,) or you can select all elements you want to have shown (that means all remaining ones are hidden).
| Certain object classes, particularly object classes of subentries, are a priori hidden in search panes and search dialogs and cannot be made visible. |
| Hiding all attributes of an object class (exactly: all attributes but the attribute "object class" that every object class has, at least if derived from object class "top") implicitly causes that object class to be hidden, too. |
Password
Here is an example of the dialog’s "Password" tab:
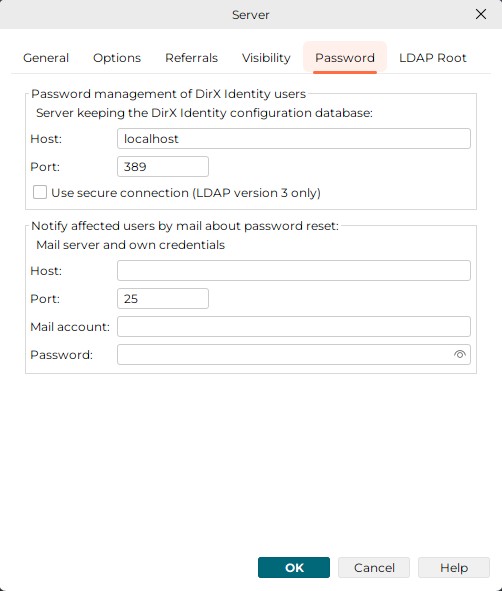
Password management of DirX Identity users
Only of interest if the server addresses a DirX Identity database. Among many other things, DirX Identity deals with DirX Identity users that are characterized by an additional password stored in the attribute dxmPassword. This password must - depending on the DirX Identity configuration - either be scrambled or two-way encrypted. If you modify the ordinary attribute userPassword through DirX Identity functionality, dxmPassword will be implicitly modified, too.
The core component of this application has generic password management functionality that is originally not DirX Identity aware. However, by completing the settings you can do here, you can have the core component behave like DirX Identity when modifying userPassword. The Host/Port fields relating to the password management of DirX Identity users are editable, if the schema contains the attribute dxmPassword (note that this can only be found out, if the schema can be read). In this case, the core component will consider this server a DirX Identity database. To be able to do so, the core component must enquire the DirX Identity configuration to find out, whether dxmPassword is to be scrambled or to be encrypted; in the latter case, also the key must be picked up. Note that the DirX Identity configuration may reside in a different server. By default, the server storing the DirX Identity database is assumed to also store the DirX Identity configuration.
If you leave the respective Host/Port fields empty or if dxmPassword cannot be detected in the schema, the core component will not implicitly deal with the attribute dxmPassword.
Furthermore, if the server keeping the DirX Identity users is set up, the mirrored administrator user must be present in the Connectivity under the RDN dxmC=Users,dxmC=DirXmetahub.
Mail notification on password reset
If the affected users are to be notified by mail on password resets, you must specify host and port of the mail server as well as your credentials, i.e. your mail account and the belonging password. Note that the format of the mail account varies depending on the mail server in use. Common formats include: "<your domain/your name>", <your email address>, <a number>.
Note that the reset password functionality is only available, if the server indicates its support in the LDAP Root DSE ("Password Policy Control"; Object Identifier, displayed directly or through tooltip: 1.3.6.1.4.1.42.2.27.8.5.1) and if the operational attribute pwdReset can be set.
See also: Property Tab "All Attributes", Change Password, Reset Password, User Password.
LDAP Root
Here is an example of the dialog’s "LDAP Root" tab:
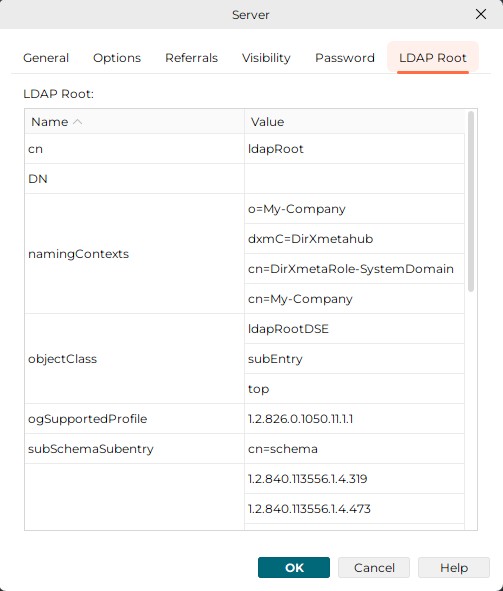
This tab displays what the server returns if asked for "LDAP Root" (which is done by reading an entry with its DN being empty, i.e. DN=""). Details may vary from server to server, mainly depending on the vendor. Refer to the server’s original documentation for properties that are not self-explanatory. Note that modifying the LDAP Root is not supported. This application uses LDAP Root itself for a number of purposes; for example to:
-
Locate the server’s schema
-
Find out what controls the server supports
Open Server/Manage Server Profiles
The "Open Server" dialog allows you to open a pre-configured server profile. It also allows you to add new and delete/edit existing server groups profiles. New profiles can also be created based on existing ones using "Copy".
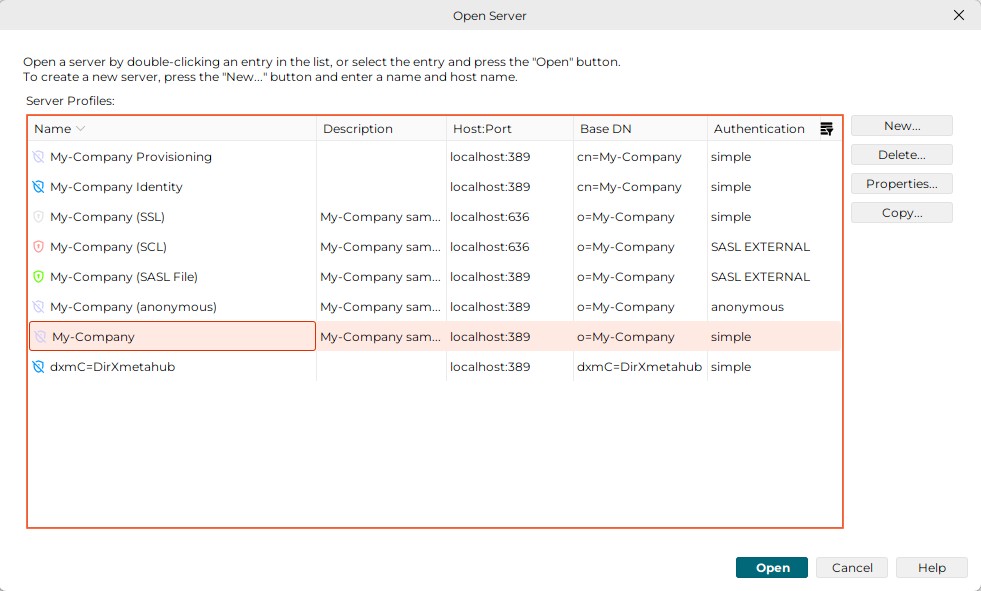
The slightly different "Manage Server Profiles" dialog may be available in the Login dialog. It has a "Close" button rather than an "Open" and a "Cancel" button, since an open button would not make sense in that context.
Advanced Components
Code Editor
The Code Editor is a special editing tool that you can use to maintain Tcl scripts, XML object descriptions, INI files, etc. It is based on RSyntaxTextArea library and provides syntax highlighting and other useful features for editing code.
The main features of the Code Editor are:
-
Syntax highlighting for a better readability of the displayed code for all common programming and scripting languages
-
Text search and replace actions
-
Undo and redo actions
-
Caret location notification below the text windows
-
Automatic detection of block ends, where a block may be a text in braces, colons or other special character combinations
-
Viewer utility for resolutions of reference blocks
It consists of the following components:
-
A main editor window
-
A toolbar whose content depends on the action to be performed (search, customize, etc.)
-
A popup menu
Main Editor Window
The main editor window displays the content of the current script. Keywords, comments, and double-quoted text are displayed in different colors. The Code Editor usually appears in read-only mode (text background is greyed). Click the Edit button at the bottom of the display to switch to write mode.
When the focus is in the main editor window, and you click the right mouse button, a popup menu appears containing all command items for text manipulation.
Under the bottom-right corner of this window, the current position (line and column) of the caret is shown.
Toolbar
The toolbar appears above the main editor window for following actions:
Find
The find toolbar consists of the following items:
-
A combo box with text field to type in the search string. The combo box contains a list of recently used search strings.
-
A button Find to search for the next (or previous) occurrence of the search string. Clicking the button again searches for the next occurrence. You can also use F3 to find the next occurrence and Shift+F3 to find the previous occurrence.
-
A checkbox Match case to define whether the search should be case-sensitive.
-
A checkbox Regex to define whether the search string is a regular expression.
-
A checkbox Whole word to define whether only whole words should be matched.
-
A checkbox Mark all to define whether all occurrences of the search string should be highlighted. Only one occurrence is highlighted when this checkbox is not checked.
-
A checkbox Wrap to define whether the search should continue at the beginning of the document when the end of the document is reached (or vice versa when searching backwards).
Replace
This toolbar consists of the following items:
-
Everything of the Find toolbar described above.
-
A combo box with text field to type in the replacement string. The combo box contains a list of recently used replacement strings.
-
A button Replace to replace the currently highlighted occurrence of the search string with the replacement string.
-
A button Replace all to replace all occurrences of the search string with the replacement string.
Customize
The customize toolbar consists of the following items:
-
A combo box Theme to select the color theme for the main editor window. See Customizing the Look and Feel on how to add new editor themes. Default is dirx-light for light mode and dirx-dark for dark mode.
-
A combo box Font to select the font for the main editor window. The fonts are those installed on your system. Default is Fira Code shipped with DirX Identity.
-
A Font size spinner to select the font size for the main editor window. Minimum value is 10, maximum is 40. Default is 14.
-
A checkbox Ligatures to enable or disable font ligatures (if supported by the selected font). Default is disabled.
-
A checkbox Kerning to enable or disable font kerning (if supported by the selected font). Default is disabled.
-
A button Reset to reset all settings to their default values.
See the respective sections below for details about these actions. To hide the toolbar, press ESC.
Popup Menu
The popup menu consists of the following items:
-
Undo (Ctrl+Z) - Undoes the last write action. When invoked again, undoes the last action before the last write action. This item is enabled only if there is an action that can be undone.
When you type a text fluidly, all characters typed until pausing are removed by the undo operation. -
Redo (Ctrl+Y) - Does the last write action again. This item is only enabled if there was already an edit action in the current edit session.
All characters typed until pausing are inserted again by the redo operation, if the text was typed fluidly. -
Cut (Ctrl+X) - This item is only enabled when a portion of text has been selected. Cuts off the selected text from the script and stores it in the clipboard.
-
Copy (Ctrl+C) - The item is only enabled when a portion of text has been selected. Copies the selected text and stores it in the clipboard.
-
Paste (Ctrl+V) - This item is only enabled when the current clipboard content can be converted to text and inserted at the current position. Converts the clipboard content to a text string and inserts this string at the current position of the caret.
-
Delete (Del) - If no text is selected, this item deletes the character right to the caret. If a portion of text is selected, this item deletes the selected text.
-
Select all (Ctrl+A) - Use this item to select the whole content of the currently displayed document. Moves the caret to the end of the document.
-
Go to line… (Ctrl+L) - Opens a prompt dialog where you can type in the line number to which the caret should be moved. After confirming the dialog by clicking on the OK button, the caret is moved to the beginning of the specified line. If the line number is out of range, an error message is shown.
-
Find (Ctrl+F) - Shows the find-related toolbar at the top of the editor window.
-
Replace (Ctrl+R) - Shows the replace-related toolbar at the top of the editor window.
-
Customize (Ctrl+M) - Shows the customize-related toolbar at the top of the editor window.
Customizing the Look and Feel
Since version 3.0.0, the Look and Feel (L&F) of this application is based on the open source FlatLaf library
The overall L&F is composed of the following resources:
Each of these sections describes how to customize the respective resource. Their settings are saved in the file <USER_HOME>/.DirXmanager/Appearance.settings. Modify or add the properties there to use your customizations. See the Customization section for each resource below.
| You may notice dxdm. prefix in the property names. This is predefined prefix for DirX Directory Manager settings. For other applications, the prefix may be different (for example, dxim. for DirX Identity Manager). |
| Do not modify the installation files in <DXDM_INSTALL_PATH>/resources/ directly. Instead, always create copies of the files you want to customize and place them in a separate folder accessible by the user running DirX Directory Manager (for example, in your home directory). This way, your customizations are preserved when you upgrade DirX Directory Manager. |
Themes
Themes define the overall appearance of the DirX Directory Manager. A theme consists of a set of color and style definitions for various UI elements. The application contains these predefined themes:
-
DirX: The path to it is <DXDM_INSTALL_PATH>/resources/themes/DirX.
You can see in this folder that there are two files, FlatLightLaf.properties and FlatDarkLaf.properties, which define the light and dark variants of the DirX theme. Each contains definitions for colors, borders, and other UI properties for almost all components.
Customization
To create a custom theme, copy both files of one of the predefined themes to a new folder, for example, <USER_HOME>/DirX/jDiscover/MyCustomTheme (the folder can be anywhere and have any name, but it must be accessible by the user running DirX Directory Manager).
Then, modify the copied files to change properties as desired. We recommend only changing the color, font and border properties, for example to match your corporate design.
To use your custom theme, open the file described in Customizing the Look and Feel and set the following properties:
dxdm.theme.directory=<PATH_TO_YOUR_CUSTOM_THEME_FOLDER> dxdm.theme.variant=LIGHT // or DARK
Fonts
Fonts define the typography used in the DirX Directory Manager. You can customize the font family, size, and other properties. The application uses the following default font settings:
-
Font Family: Montserrat
-
Font Size: 12pt
For monospaced fonts (used in code editors and log viewers), the default is Fira Code.
Both of these fonts are included in the installation package, located in the path <DXDM_INSTALL_PATH>/resources/fonts/. You may want to install these fonts on your system to ensure consistent appearance.
Customization
| Only TTF files are supported. Do not use other formats like OTF or WOFF. |
If you want to use custom fonts, but not install them on the system, define a folder containing your font files. You can place this folder anywhere accessible by the user running DirX Directory Manager, for example, <USER_HOME>/DirX/jDiscover/MyFonts. The font files can be split into subfolders as needed.
Then, open the file described in Customizing the Look and Feel and set the following property:
dxdm.font.directory=<PATH_TO_YOUR_FONT_FOLDER>
This setting makes DirX Directory Manager load all the fonts from the specified folder.
To change the default fonts used in the application, set the following property in your theme files (see Themes):
defaultFont=<DEFAULT_SIZE> "<YOUR_FONT_FAMILY>" // for example '12 "Montserrat"'
| At some places in the application, the fonts are not customizable (for example some HTML pages). |
Icons
Icons define the visual symbols used throughout the DirX Directory Manager. The application uses a set of SVG icons located in the path <DXDM_INSTALL_PATH>/resources/icons/. You can find the DirX Material icon set there.
Customization
| Only SVG icons are supported. Do not use other formats like PNG or ICO. |
To use custom icons, define a folder containing your icon files (icon set). You can place this folder anywhere accessible by the user running DirX Directory Manager, for example, <USER_HOME>/DirX/jDiscover/MyIconsSet. The icons must be named exactly as the original icons to replace them correctly. Icons not defined in you custom folder will fall back to the default ones.
Then, open the file described in Customizing the Look and Feel and set the following property:
dxdm.iconsSet.directory=<PATH_TO_YOUR_ICONS_SET_FOLDER>
Logos
Logos are used in the Logo Panel and other prominent places. The default logo is located in the path <DXDM_INSTALL_PATH>/resources/logos. The default is dirx-directory.svg.
Customization
To use custom logo, simply place your custom logo’s file in a folder accessible by the user running DirX Directory Manager, for example, <USER_HOME>/DirX/jDiscover/MyLogos. Then, open the file described in Customizing the Look and Feel and set the following property:
dxdm.logo.file=<PATH_TO_YOUR_LOGO_FILE>
| Only SVG logos are supported. Do not use other formats like PNG or ICO. |
Editor themes
The code editor used across the DirX Directory Manager (for example in Tcl script editing) supports different color themes. These themes are defined in the path <DXDM_INSTALL_PATH>/resources/editor/ as XML files based on theme.dtd. You can select the desired theme from the Customize toolbar in the code editor (see Code Editor Toolbar Customize).
Customization
To add custom editor themes, create XML files based on theme.dtd (best to use one of the predefined files) and place them in a folder accessible by the user running DirX Directory Manager, for example, <USER_HOME>/DirX/jDiscover/MyEditorThemes. Then, open the file described in Customizing the Look and Feel and set the following property:
dxdm.editor.directory=<PATH_TO_YOUR_EDITOR_THEMES_FOLDER>
This setting makes DirX Directory Manager load all the editor themes from the specified folder (plus default ones).
Troubleshooting
This section describes some common problems and their solutions.
Scale of the application window is incorrect
If the scale of the application window is incorrect (for example, too small or too large), you can adjust it by setting one of these environment variables:
-
DXDM_UI_SCALE=<VALUE>- Used for DirX Directory Manager only. Has precedence over the other variables. -
JDISCOVER_UI_SCALE=<VALUE>- Used for all jDiscover-based applications that support it.
The reasonable values for <VALUE> are between 0.5 and 2.0, where 1.0 is the default scale.
You must restart the application if you are currently running it.
Login
-
IP filtering (to be configured in the LDAP configuration subentry) offers a powerful way to keep clients from connecting to the server from unwanted IP addresses. However, improper settings may lockout authorized users including yourself, too.
If the DirX Directory Manager plug-in is installed, you may have access to the LDAP configuration subentry from within this application (probably from a different IP address); otherwise use a tool provided by the server like dirxadm -
SSL is a powerful way to secure the client/server communication. It presumes however that a keystore with a suitable certificate is configured.
Retrieval operations
-
Access control may hide the existence of any subset of the directory information. So, not finding certain entries or attributes in a read/search/export operation does not necessarily mean that those entries or attributes are not there.
-
Access control may cause the entire search functionality to be unavailable. Typical reason: Schema cannot be read.
-
If tree browsing does not work, check, if the naming context is administered in the LAP Root DSE.
-
If an administrative limit like time or size limit restricts the search result, the entries returned are not necessarily the alphabetically leading ones. So, in this case it is absolutely normal if an entry you are expecting because it matches your search criteria does not appear in the search result list.
Administrative operations like Add/Modify/Rename/Delete
If you run your directory with shadowing in order to balance communications traffic and increase reliability, be aware of the following possible effects: when adding/modifying/renaming/deleting an entry while connected to a shadow DSA, the operation may appear to have failed, since the entry might be missing/out-dated/still there when searching for it later on. This is because administrative operations always affect the master, while the search operation may address a shadow that is not yet up to date
Moreover, if the server does not support simple paging, a delete subtree may have trouble completing at all within a reasonable period of time, since it has to search the shadow for entries to be deleted and might receive the same entries again and again, as long as the shadow is not updated.
These effects are mitigated if you:
-
Connect directly to the master (this may however not always be viable).
-
Have the master update the shadow "on change". In this case, the shadow should become synchronized rather quickly (this may not always be viable either).
-
Set up dedicated LDAP servers to be contacted by administrators and make sure they directly address the master DSA or the service control "Don’t use copy" (corresponding LDAP configuration subentry) is set to "true" for all operations.